What is QEHU Virus?
QEHU a type of STOP/Djvu ransomware, encrypts files on computers, making them inaccessible. It targets a variety of file types, appending a “.qehu” extension to them, which renders the files unusable without a decryption key.
After infecting a system, Qehu demands a ransom in Bitcoin for decrypting files. Victims find a “_readme.txt” guide on desktops and within folders that instructs them on how to make the payment, though payment does not guarantee recovery.
The virus employs the Salsa20 encryption algorithm, which complicates decryption efforts without the attacker’s cooperation. However, if Qehu cannot connect to its server before starting the encryption, it uses a standard offline key, offering a potential avenue for decryption.
Below, an image shows the appearance of encrypted files, marked by the “.qehu” extension:
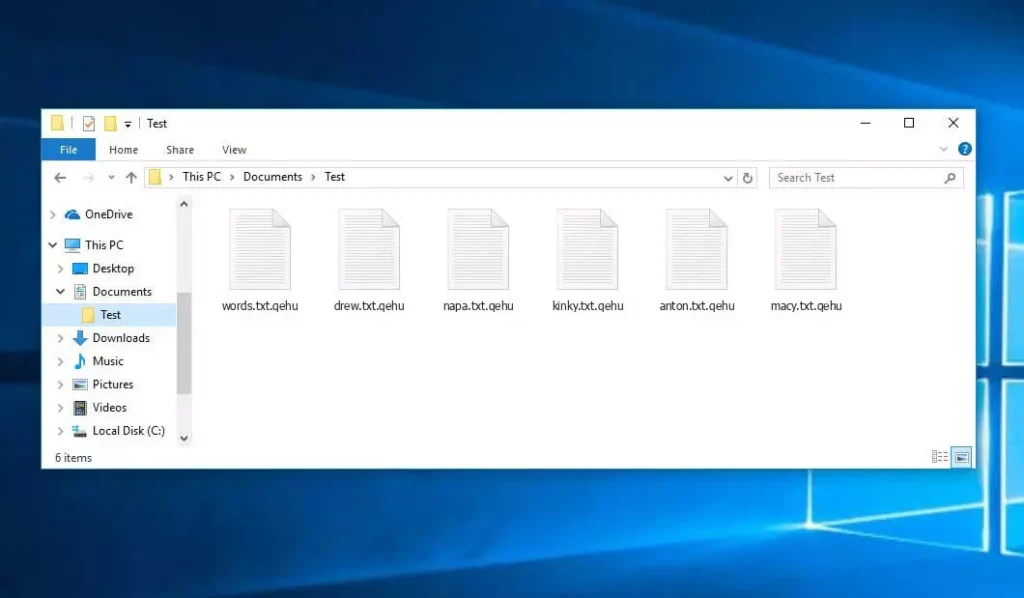
Encrypted Qehu Files: Windows PC
| Name | Qehu Virus |
| Family 1 | STOP/Djvu Ransomware |
| Extension | .qehu |
| Ransomware note | _readme.txt |
| Ransom | From $499 to $999 (in Bitcoins) |
| Contact | support@freshingmail.top, datarestorehelpyou@airmail.cc |
| Symptoms |
|
| Recovery | Start recovery with a comprehensive antivirus scan. Although not all files may be recoverable, our guide outlines several potential methods to regain access to encrypted files. |
Qehu Virus Overview
Qehu ransomware executes a set of procedures on a victim’s computer upon arrival. It launches winupdate.exe as one of the initial processes, which displays a fraudulent Windows update prompt during the attack to convince the victim their PC is slowing down due to a Windows update.
Meanwhile, the ransomware runs another process (named with 4 random chars), which begins scanning the computer for target files and encrypting them. It then removes Volume Shadow Copies from the system using the following CMD command:
vssadmin.exe Delete Shadows /All /Quiet
Once removed, it becomes impossible to retrieve the computer’s previous state using System Restore Points. The ransomware operators eliminate any built-in Windows approaches that could help the victim restore files for free. Additionally, they modify the Windows HOSTS file by adding a list of domains to it, redirecting them to the localhost IP, which results in a DNS_PROBE_FINISHED_NXDOMAIN error when the victim tries to open one of the blocked websites.
We’ve observed that the ransomware tries to restrict websites from publishing various how-to guides for computer users. Clearly, by limiting specific domains, the attackers attempt to prevent victims from accessing relevant and helpful online information related to ransomware attacks. The virus also stores two .txt files on the victim’s computer providing attack-related information – the public key of this victim and a personal ID, named bowsakkdestx.txt and PersonalID.txt.
After all these modifications, the malware doesn’t stop. Variants of STOP/DJVU often deploy the Vidar password-stealing Trojan on compromised systems, a threat with a vast list of capabilities, including:
- Infiltrating and executing malware on the victim’s computer to gain unauthorized access.
- Obtaining unauthorized access to login credentials of Steam, Telegram, and Skype.
- Manipulating and viewing files on the victim’s computer without their consent.
- Stealing cryptocurrency wallets from the victim’s system.
- Granting the hackers remote control over the victim’s computer for various malicious purposes.
- Extracting sensitive information such as browser cookies, saved passwords, and browsing history.
The cryptography algorithm in STOP/Djvu ransomware is Salse20. So, once it encrypts your data with an online decryption key, the chances of getting your files back become quite low. This key is unique for each victim, and finding a suitable one would take an impractical amount of time.
Retrieving the online key in another way is also nearly impossible. The hackers spread the Qehu infection on the server where it is stored. To receive the decrypting code, the payment should be $999. For payment details, the victims must contact the hackers by email (support@fishmail.top).
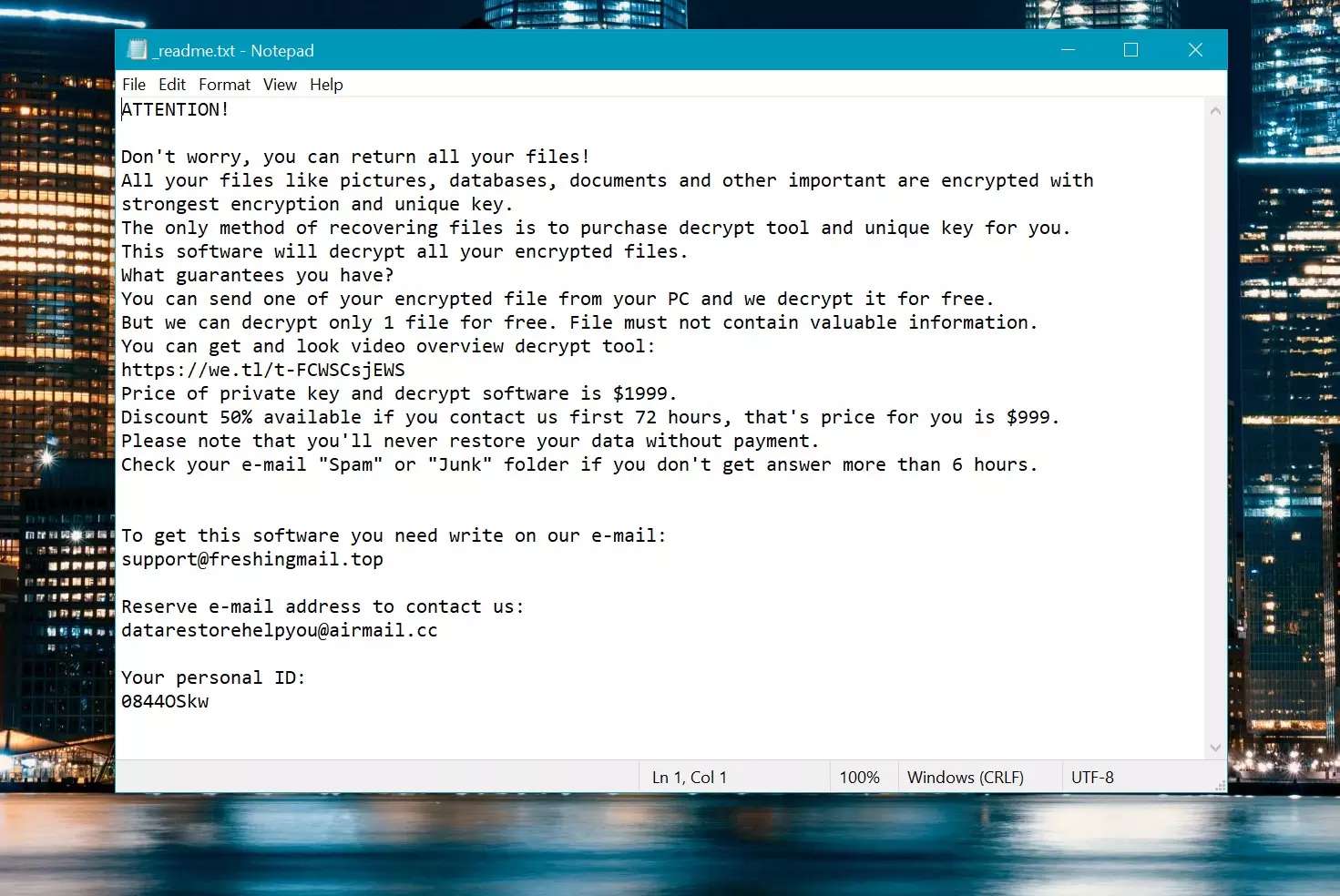
Ransom Note: _readme.txt
How To Remove?
Remove Qehu Virus with Gridinsoft Anti-Malware
We have also been using this software on our systems ever since, and it has always been successful in detecting viruses. It has blocked the most common Ransomware as shown from our tests with the software, and we assure you that it can remove Qehu Virus as well as other malware hiding on your computer.

To use Gridinsoft for remove malicious threats, follow the steps below:
1. Begin by downloading Gridinsoft Anti-Malware, accessible via the blue button below or directly from the official website gridinsoft.com.
2.Once the Gridinsoft setup file (setup-gridinsoft-fix.exe) is downloaded, execute it by clicking on the file. Follow the installation setup wizard's instructions diligently.

3. Access the "Scan Tab" on the application's start screen and launch a comprehensive "Full Scan" to examine your entire computer. This inclusive scan encompasses the memory, startup items, the registry, services, drivers, and all files, ensuring that it detects malware hidden in all possible locations.
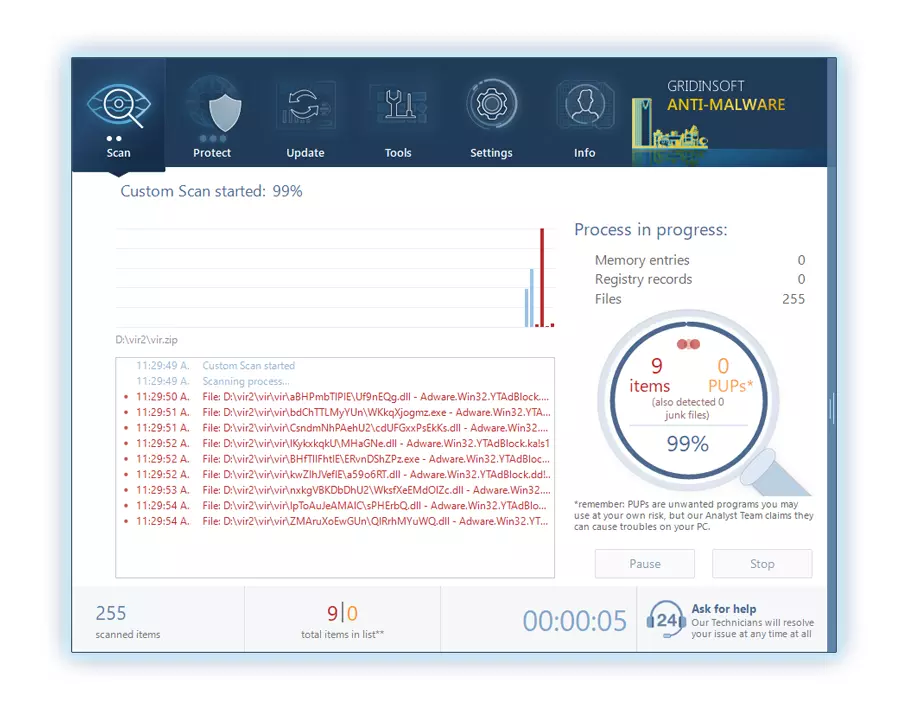
Be patient, as the scan duration depends on the number of files and your computer's hardware capabilities. Use this time to relax or attend to other tasks.
4. Upon completion, Anti-Malware will present a detailed report containing all the detected malicious items and threats on your PC.
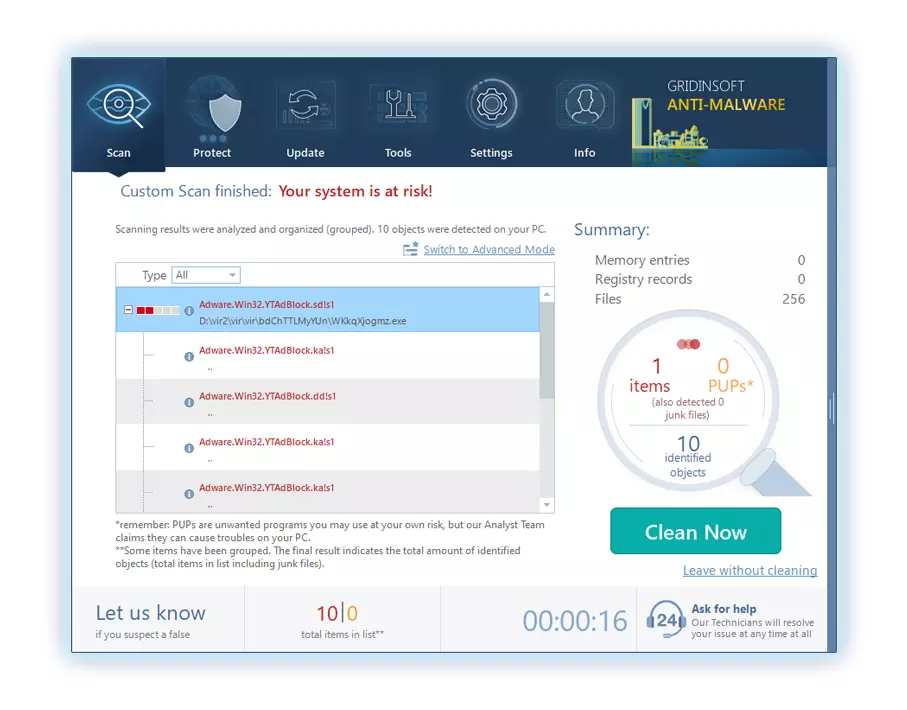
5. Select all the identified items from the report and confidently click the "Clean Now" button. This action will safely remove the malicious files from your computer, transferring them to the secure quarantine zone of the anti-malware program to prevent any further harmful actions.
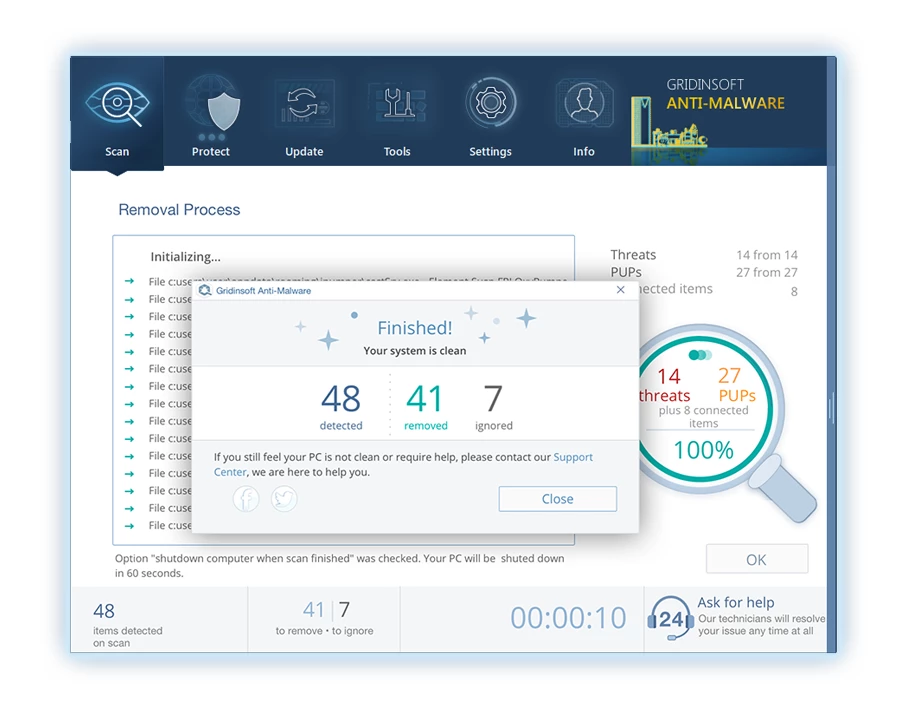
6. If prompted, restart your computer to finalize the full system scan procedure. This step is crucial to ensure thorough removal of any remaining threats. After the restart, Gridinsoft Anti-Malware will open and display a message confirming the completion of the scan.
Remember Gridinsoft offers a 6-day free trial. This means you can take advantage of the trial period at no cost to experience the full benefits of the software and prevent any future malware infections on your system. Embrace this opportunity to fortify your computer's security without any financial commitment.
Video Guide
How To Decrypt .qehu Files?
First, try deleting the “.qehu” extension from a few big files and then opening them. This malware struggles with the encryption of large files. The virus either failed to lock the file upon access or encountered a bug and omitted to add the file marker. If your files exceed 2GB in size, the latter scenario is more probable.
Criminals released the newest extensions around the end of August 2019 after making several changes.
The changes by the criminals rendered STOPDecrypter unsupported, leading to its replacement with the Emsisoft Decryptor for STOP Djvu Ransomware developed by Emsisoft.
- Download and Run the Decryption Tool: Download decryption tool. Ensure you run the decryption utility as an administrator and agree to the license terms that appear by clicking the “Yes” button. Upon accepting the license terms.
- Select Folders for Decryption: The decryptor, by default, automatically selects directories on connected and network drives for decryption. Use the “Add” button to select additional locations. Depending on the malware family, decryptors offer various options, which you can toggle on or off in the Options tab. Below, you will find a detailed list of the currently active options.
- Initiate Decryption by Clicking on the “Decrypt” Button. After adding all desired locations to the list, click the “Decrypt” button to start the decryption process. The decryptor will inform you upon completing the decryption process. If needed for documentation, you can save the report by clicking the “Save log” button. It’s also possible to copy the report to your clipboard for pasting into emails or messages.
How to Restore .qehu Files?
In some cases, ransomware fails to encrypt your files…
The Qehu ransomware encryption process involves encrypting each file byte-by-byte, creating a duplicate, and then deleting (not overwriting) the original file. This deletion means the physical disk no longer lists the file in its system, although the original file remains on the drive. The sector that held the file might still contain it, but since the system does not list it, new data can overwrite it. However, special software can recover your files.
Realizing it was an online algorithm, I knew recovering my encrypted files was impossible. My backup drive, connected during the infection, seemed infected as well. Every folder on my backup drive appeared encrypted. Despite this, I managed to recover nearly 80% of my 2TB storage.
Examining the folders, I found ransom notes in each. Opening some revealed that only files not in subfolders were encrypted. Delving into subfolders in other folders, I discovered unencrypted files. Unlike my C and D drives where every folder, including subfolders, was encrypted, my backup drive’s subfolders saved 80% of my data.
I consider finding this loophole on my backup drive fortunate. Additionally, I recovered another 10% of my data from a hard drive on a different PC. Thus, my advice for using a backup drive is to create subfolders. It was partly luck, but also misfortune that the virus struck during file transfers from my backup.
I hope this experience can assist others in similar predicaments.
Jamie NewlandRecover Qehu Files with PhotoRec
PhotoRec, designed for file recovery from damaged disks or accidental deletion, now supports restoring 400 file types, making it useful after a Qehu attack.
First, download PhotoRec. It’s free, but the developer offers no guarantee for file restoration. PhotoRec comes packaged with TestDisk, another tool from the same developer, under the TestDisk name. However, PhotoRec is included within the archive.
To start PhotoRec, open the “qphotorec_win.exe” file. No installation is necessary as the program contains all required files, allowing it to run from a USB drive.







Leave a Comment