Verification.exe is a malicious process found on Windows systems. It may serve as a miner or pose as legitimate while being malicious. This malicious software is designed to execute various harmful operations on compromised systems. Such actions encompass data theft, deployment of further malware, and facilitation of unauthorized access and control by attackers.
Verification.exe Overview
The Verification.exe Trojan is a harmful program that can cause various issues on your compromised computer. It can be used to steal personal data, install other malware, and provide unauthorized access to attackers. This Trojan carries out various malicious activities, such as downloading and installing other malware, exploiting your computer for click fraud, logging keystrokes, and tracking visited sites.
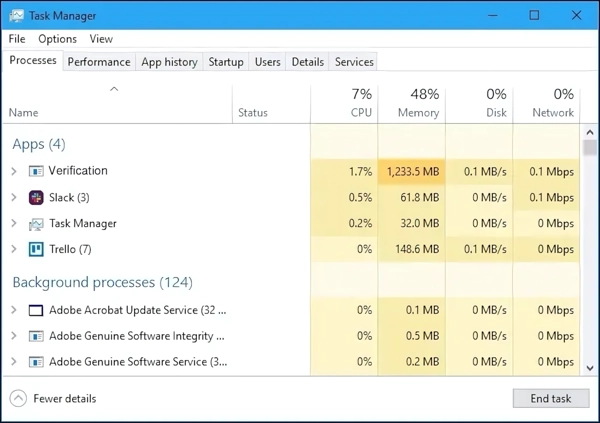
Verification.exe process in the Task manager
It can also transmit your PC information, like usernames and browsing history, to remote malicious entities, grant remote access to your PC, display advertisements, and redirect browser search queries. Additionally, it can utilize your computer resources for cryptocurrency mining. It is crucial to be aware of this Trojan’s potential threats and take steps to protect your computer from such attacks.
Threat Summary
| Name | Verification.exe |
| Threat Type | Trojan Virus |
| Details | Steals personal data, brings other malicious programs, mangles system security, can mine cryptocurrencies. |
The reason why this malware has picked the Verification.exe name is rather simple – to blend in with other background process. This typically makes the user think it is legit. However, when it takes too much system resources, or runs regardless of what program is running, then it’s time for raising the alarm.
How did I get infected?
The Verification.exe can infiltrate your system in various ways. One standard method is through malicious ads that may appear while browsing the internet. These ads can trick you into clicking on a link or downloading an attachment that contains the Trojan. Another way the malware can spread is through spam emails, which may contain infected attachments. It can also take advantage of your operating system or software vulnerabilities to gain access to your system.
Another distribution method is through pirated software or illegal downloads. Most pirated software requires mandatory disabling of the security software on the device. This is because the mechanics of hacking tools are similar to those of malware, making it ideal for spreading it. So, supposeå you are downloading software from an untrusted source or engaging in software piracy. In that case, you are putting your system at risk.
Remove Verification.exe with Gridinsoft Anti-Malware
We have also been using this software on our systems ever since, and it has always been successful in detecting viruses. It has blocked the most common Trojans as shown from our tests with the software, and we assure you that it can remove Verification.exe as well as other malware hiding on your computer.

To use Gridinsoft for remove malicious threats, follow the steps below:
1. Begin by downloading Gridinsoft Anti-Malware, accessible via the blue button below or directly from the official website gridinsoft.com.
2.Once the Gridinsoft setup file (setup-gridinsoft-fix.exe) is downloaded, execute it by clicking on the file. Follow the installation setup wizard's instructions diligently.

3. Access the "Scan Tab" on the application's start screen and launch a comprehensive "Full Scan" to examine your entire computer. This inclusive scan encompasses the memory, startup items, the registry, services, drivers, and all files, ensuring that it detects malware hidden in all possible locations.
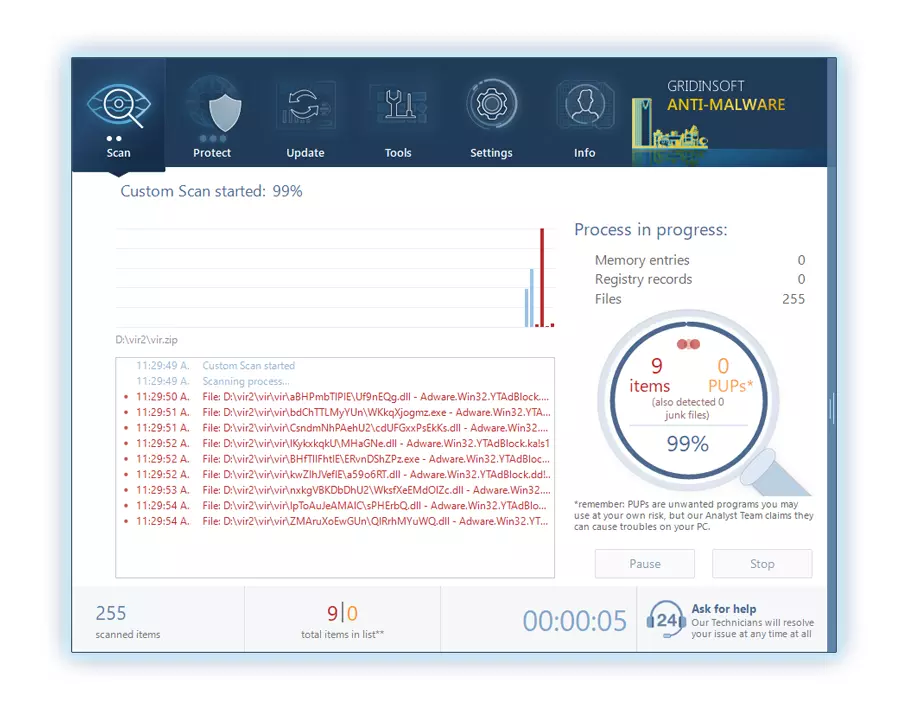
Be patient, as the scan duration depends on the number of files and your computer's hardware capabilities. Use this time to relax or attend to other tasks.
4. Upon completion, Anti-Malware will present a detailed report containing all the detected malicious items and threats on your PC.
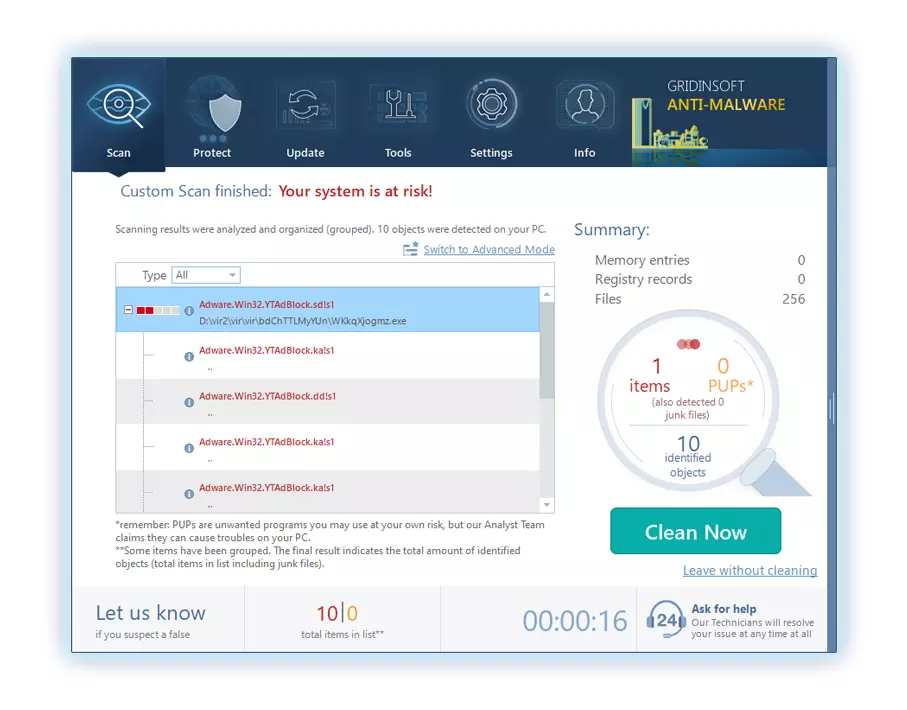
5. Select all the identified items from the report and confidently click the "Clean Now" button. This action will safely remove the malicious files from your computer, transferring them to the secure quarantine zone of the anti-malware program to prevent any further harmful actions.
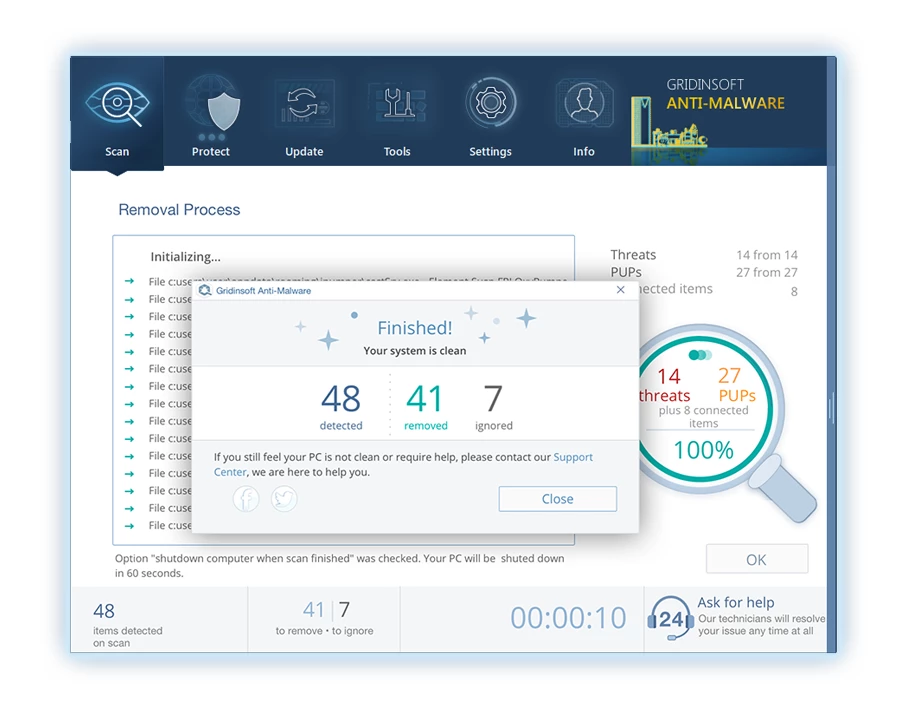
6. If prompted, restart your computer to finalize the full system scan procedure. This step is crucial to ensure thorough removal of any remaining threats. After the restart, Gridinsoft Anti-Malware will open and display a message confirming the completion of the scan.
Remember Gridinsoft offers a 6-day free trial. This means you can take advantage of the trial period at no cost to experience the full benefits of the software and prevent any future malware infections on your system. Embrace this opportunity to fortify your computer's security without any financial commitment.






Leave a Comment