Trojan:Script/Phonzy.B!ml is a detection name used by Microsoft Defender to detect a script-based loader malware. As the detection comes from the AI detection system, there is a chance of it being a false positive.
The more time such a threat remains active, the more malware it can inject into it. Phonzy.B!ml trojan in particular aims at deploying banking trojans that steal online banking services’ credentials. Removing it should be a primary concern.
Trojan:Script/Phonzy.B!ml Summary
As I just said, Trojan:Script/Phonzy.B!ml operates as a malware downloader, facilitating the injection of additional viruses into the system. It commonly adjusts system configurations, particularly networking settings and Microsoft Defender. This makes it particularly hard to remove without using additional security tools.
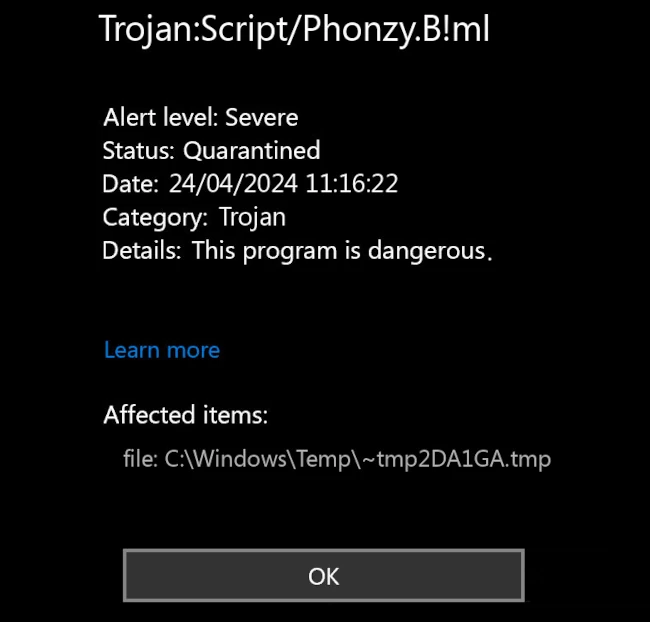
Phonzy.B!ml detection image
Main target of Phonzy.B!ml activity is deploying banking trojans, as far as my observations go. Using DLL hijacking techniques, this malware hooks up malicious programs, effectively granting them max privileges. Following the first post-injection steps, this malware connects to the command servers and waits for the command.
Threat Summary:
| Name | Phonzy Trojan |
| Detection | Trojan:Script/Phonzy.B!ml |
| Details | Phonzy acts as a downloader for other malware, performing initial reconnaissance and weakening the system security. |
At the same time, nothing restricts Phonzy from delivering other malware. Everything boils down to who pays, and the rest is unimportant to this malware’s masters. Using the same methods, the malware can deploy spyware, backdoors and even ransomware. The effects of all this malware activity are unpleasant, to say the least – lost online accounts, encrypted files and third-parties being able to control the system remotely.
How Did Trojan:Script/Phonzy.B!ml Get Into My System?
Most often, malware like Phonzy.B!ml arrives to the system as a part of cracked software or a program downloaded from a shady source. Users can see advertisements in search engines that pose as original software downloading pages, but are in fact malignant copies. Cracked software, on the other hand, is typically spread on dedicated websites.
It is worth noting that hackers constantly seek for new malware spreading ways. Either by modifying already existing approaches, or targeting some new trends, they achieve much higher infection rates. Users should keep track of the latest trends and stay away from all the related elements.
Is it a False Positive?
Microsoft’s detection naming convention reveals that the “!ml” designation stands for “machine learning,” indicating detection by their AI engine. While effective, it necessitates confirmation from a signature detection system to avoid false positives. When none is available, the built-in antivirus may display a detection of a completely legit file.
The problem here is that it is not easy to understand whether it is a real of a false detection. Differentiating between them is particularly hard as modern malware often conceals itself among legitimate files. That is yet another reason why I recommend using a different anti-malware tool.
Remove Trojan:Script/Phonzy.B!ml with Gridinsoft Anti-Malware
We have also been using this software on our systems ever since, and it has always been successful in detecting viruses. It has blocked the most common Trojan Viruses as shown from our tests with the software, and we assure you that it can remove Trojan:Script/Phonzy.B!ml as well as other malware hiding on your computer.

To use Gridinsoft for remove malicious threats, follow the steps below:
1. Begin by downloading Gridinsoft Anti-Malware, accessible via the blue button below or directly from the official website gridinsoft.com.
2.Once the Gridinsoft setup file (setup-gridinsoft-fix.exe) is downloaded, execute it by clicking on the file. Follow the installation setup wizard's instructions diligently.

3. Access the "Scan Tab" on the application's start screen and launch a comprehensive "Full Scan" to examine your entire computer. This inclusive scan encompasses the memory, startup items, the registry, services, drivers, and all files, ensuring that it detects malware hidden in all possible locations.
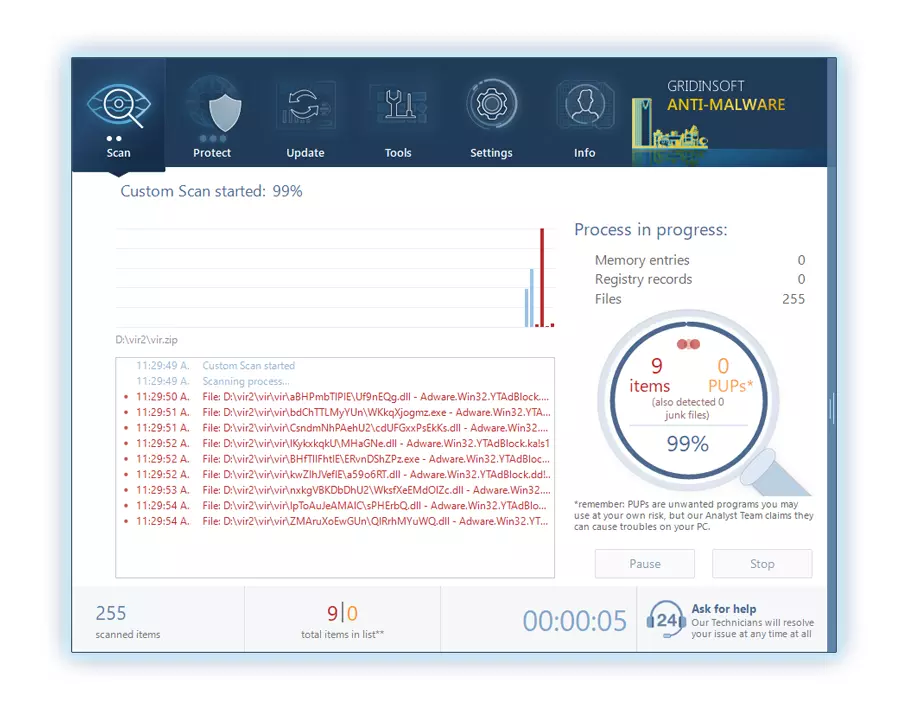
Be patient, as the scan duration depends on the number of files and your computer's hardware capabilities. Use this time to relax or attend to other tasks.
4. Upon completion, Anti-Malware will present a detailed report containing all the detected malicious items and threats on your PC.
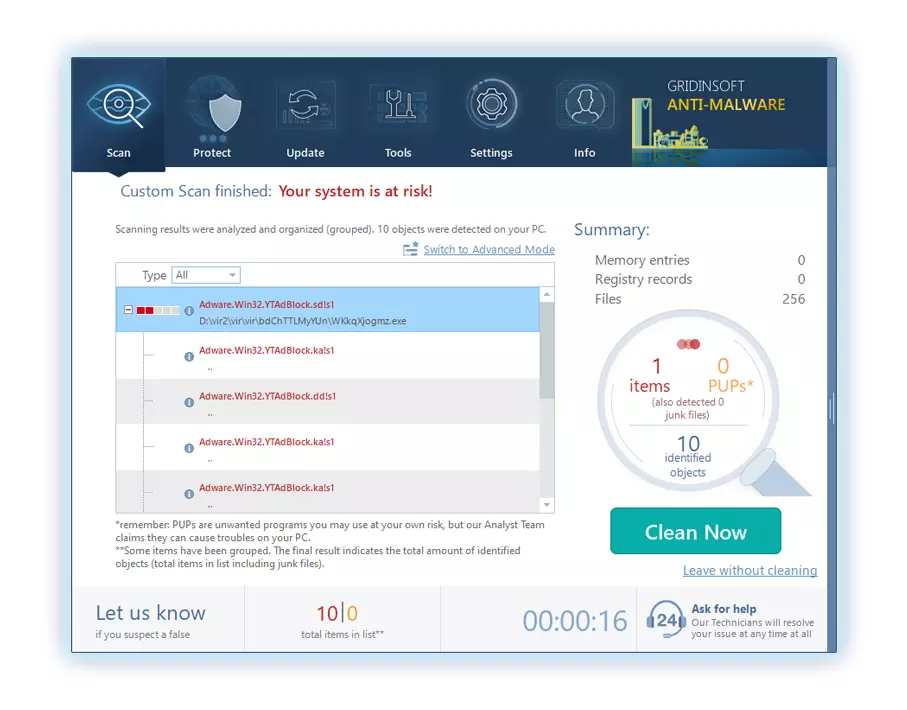
5. Select all the identified items from the report and confidently click the "Clean Now" button. This action will safely remove the malicious files from your computer, transferring them to the secure quarantine zone of the anti-malware program to prevent any further harmful actions.
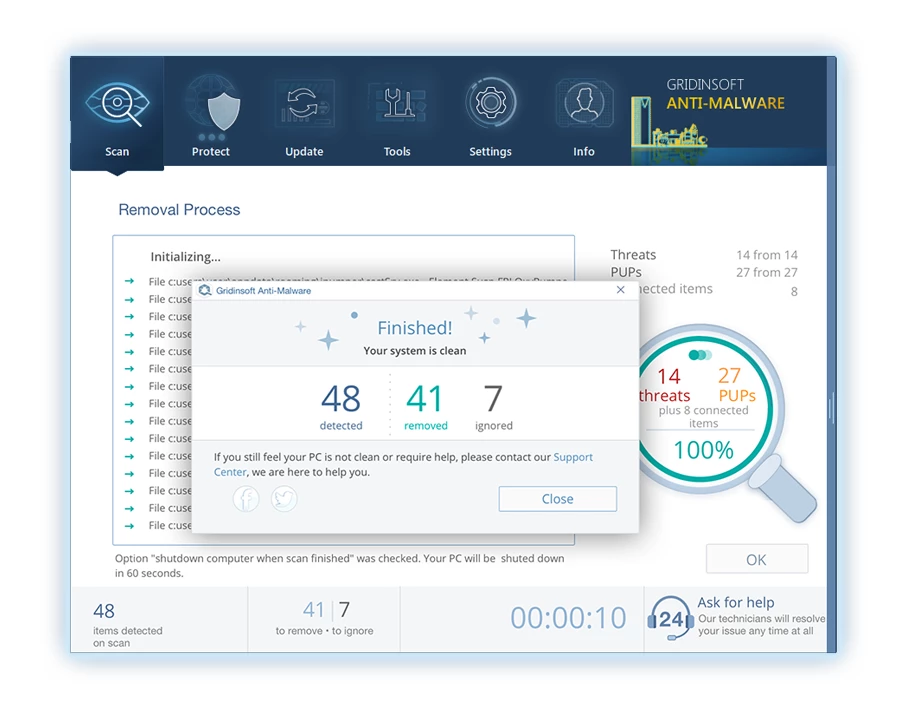
6. If prompted, restart your computer to finalize the full system scan procedure. This step is crucial to ensure thorough removal of any remaining threats. After the restart, Gridinsoft Anti-Malware will open and display a message confirming the completion of the scan.
Remember Gridinsoft offers a 6-day free trial. This means you can take advantage of the trial period at no cost to experience the full benefits of the software and prevent any future malware infections on your system. Embrace this opportunity to fortify your computer's security without any financial commitment.




Leave a Comment