O Trojan Wacatac é identificado pelo Microsoft Defender como abrangendo uma variedade de ameaças que combinam capacidades de spyware com a capacidade de entregar malware. Reconhecido pelo seu alto risco, Wacatac exige manuseio cauteloso devido à sua natureza perigosa.
Compreendendo Wacatac
WACATAC serve como um rótulo para um amplo espectro de software malicioso caracterizado por sua funcionalidade de spyware e seu papel como distribuidor ou conta-gotas de malware. Essa funcionalidade dupla prevalece em muitas instâncias de malware modernas, tornando as detecções de Wacatac cada vez mais comuns.
Ocasionalmente, o que é detectado pode ser principalmente um conta-gotas, em vez de um spyware ou um ladrão de dados. Os droppers normalmente coletam informações do sistema para identificar o dispositivo alvo, um comportamento que o Microsoft Defender pode interpretar como coleta de dados. Embora esta recolha de dados seja menos abrangente, isso ressalta a lógica por trás da detecção.
Visão geral da ameaça
| Nome | troiano:Win32/Wacatac |
| Comportamento | Roubo de dados, Distribuição de malware |
| Categoria de malware | Spyware, Ladrão de informações, Trojan bancário, Conta-gotas |
| Métodos de transmissão | Anexos de e-mail maliciosos, software não autorizado de fontes não oficiais |
| Variantes | troiano:Win32/wacatac.b!ml, troiano:Win32/wacatac.h!ml, troiano:Script/Wacatac.H!ml |
Os riscos representados pelo Trojan:Win32/Wacatac
As principais ameaças do Wacatac incluem seus recursos de spyware – alarmantes para a privacidade do usuário, pois captura senhas, arquivos de cookies, e tokens de sessão. Seu papel como conta-gotas agrava o risco ao introduzir malware adicional, aumentando assim os atacantes’ ganho.
Certas variantes do Wacatac têm como alvo áreas específicas, como carteiras de criptomoedas ou serviços bancários online, negociar roubo geral pelo potencial de dano financeiro significativo. Apesar disso, os invasores podem facilmente associar spyware padrão a trojans bancários, ladrões de criptografia, ou ransomware como carga secundária.
Famílias de malware detectadas como Trojan Wacatac
O Wacatac não está confinado a uma única família de malware, mas inclui vários tipos reconhecidos pelas suas características comuns.. O Microsoft Defender identifica frequentemente as seguintes famílias sob a designação Wacatac:
| Amadey conta-gotas | Atualmente entre os malwares mais ativos, usado para distribuir Vidar, Ladrões de RedLine, e ransomware STOP/Djvu. Ocasionalmente entrega criptomineradores enquanto coletando informações básicas do sistema. |
| Ladrão de prepúcio | Inicialmente um ladrão de dados, Gozi foi posteriormente aprimorado com recursos de distribuição de malware. Funciona principalmente como spyware. |
| A emoção (Época 4 variantes) | Um malware notório conhecido por combinar funções de conta-gotas e ladrões. Embora o Defender normalmente o classifique como Sabsik, mudanças na época 4 variante provavelmente alterou sua assinatura para se parecer mais com Wacatac. |
| QakBot | Um malware de longa data usado principalmente em ataques direcionados para reconhecimento e movimentação lateral. Sua rede era recentemente desmontado, potencialmente sinalizando um ressurgimento iminente. |
| Formulário | Também conhecido como xLoader, ativo desde 2016, combina funções de ladrão e conta-gotas, mas é menos famoso que o Emotet. |
Eliminando o Trojan Wacatac
Wacatac estabelece raízes profundas após a infecção, tornando a remoção manual um desafio. Esse comportamento furtivo é típico de malware que busca evitar a detecção. Como tal, utilizar uma ferramenta anti-malware é aconselhável para remoção completa.
Antimalware GridinSoft destaca-se como uma solução eficaz, graças ao seu banco de dados constantemente atualizado e aos sofisticados recursos de detecção heurística, garantindo a identificação e eliminação das mais recentes ameaças de malware.
Remova o cavalo de Troia Wacatac com Gridinsoft Anti-Malware
Também temos usado este software em nossos sistemas desde, e sempre teve sucesso na detecção de vírus. Ele bloqueou os Trojans mais comuns como mostrado em nossos testes com o software, e garantimos que ele pode remover o Trojan Wacatac, bem como outros malwares escondidos em seu computador.

Para usar Gridinsoft para remover ameaças maliciosas, Siga os passos abaixo:
1. Comece baixando Gridinsoft Anti-Malware, acessível através do botão azul abaixo ou diretamente do site oficial gridinsoft. com.
2.Assim que o arquivo de configuração do Gridinsoft (setup-gridinsoft-fix.exe) foi baixado, execute-o clicando no arquivo. Follow the installation setup wizard's instructions diligently.

3. Acesse o "Guia Digitalizar" on the application's start screen and launch a comprehensive "Verificação completa" para examinar todo o seu computador. Esta varredura inclusiva abrange a memória, itens de inicialização, o registro, Serviços, motoristas, e todos os arquivos, garantindo que ele detecte malware oculto em todos os locais possíveis.
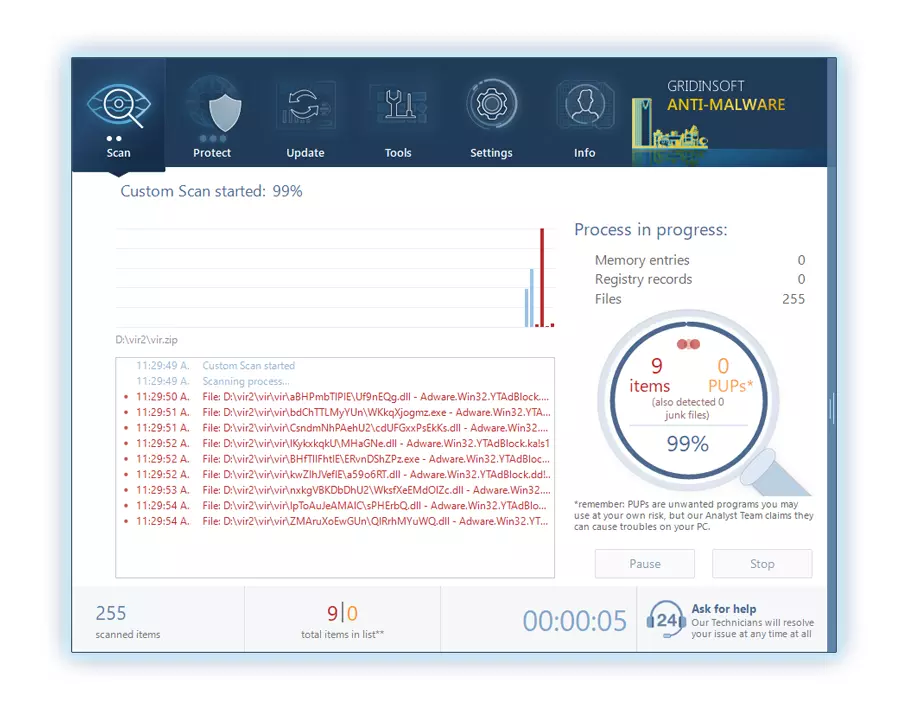
Ser paciente, as the scan duration depends on the number of files and your computer's hardware capabilities. Use esse tempo para relaxar ou realizar outras tarefas.
4. Após a conclusão, O Anti-Malware apresentará um relatório detalhado contendo todos os itens maliciosos e ameaças detectados em seu PC.
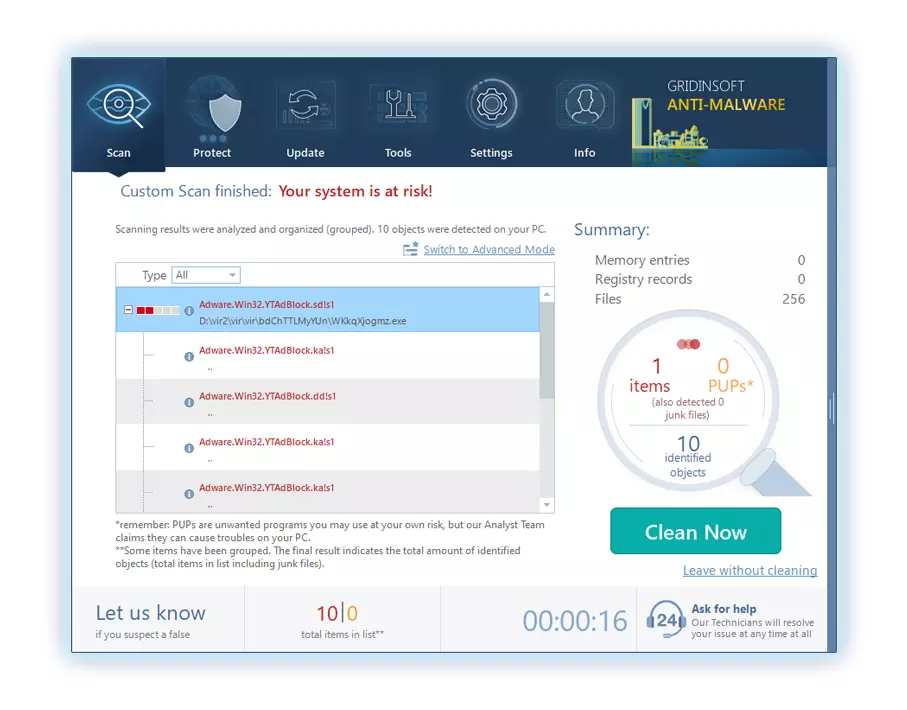
5. Selecione todos os itens identificados no relatório e clique com segurança no "Limpa agora" botão. Esta ação removerá com segurança os arquivos maliciosos do seu computador, transferindo-os para a zona de quarentena segura do programa anti-malware para evitar quaisquer outras ações prejudiciais.
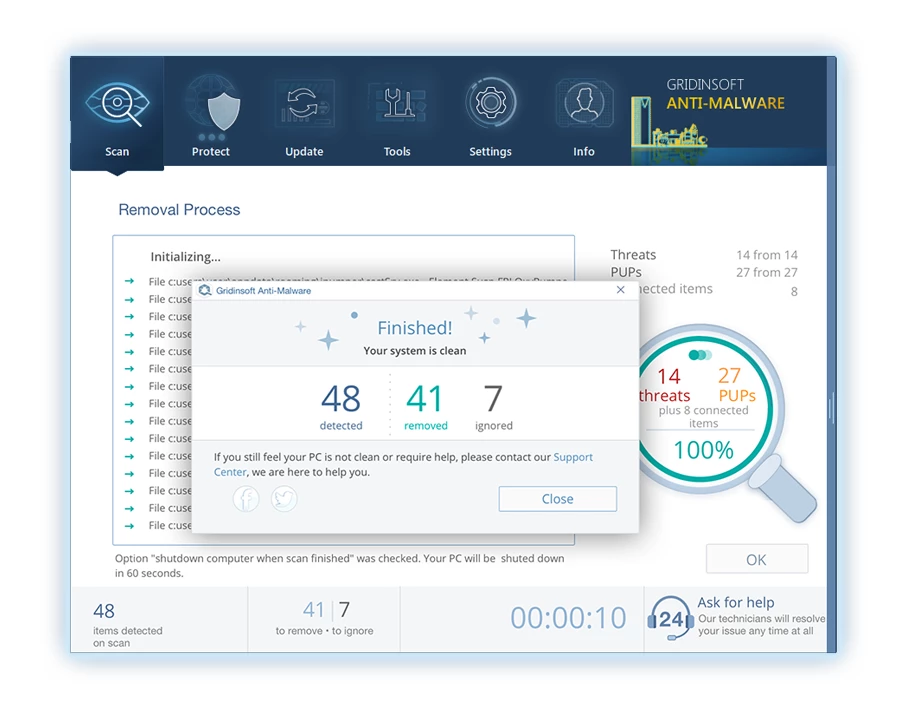
6. Se solicitado, reinicie o seu computador para finalizar o procedimento de verificação completa do sistema. Esta etapa é crucial para garantir a remoção completa de quaisquer ameaças remanescentes. Após o reinício, O Gridinsoft Anti-Malware abrirá e exibirá uma mensagem confirmando a conclusão da verificação.
Lembre-se de que Gridinsoft oferece um teste gratuito de 6 dias. Isso significa que você pode aproveitar o período de teste sem nenhum custo para experimentar todos os benefícios do software e evitar futuras infecções por malware em seu sistema.. Embrace this opportunity to fortify your computer's security without any financial commitment.
Perguntas frequentes
🤔 O que é Trojan Wacatac?
WACATAC, também conhecido como Trojan:Win32/Wacatac, é um malware que realiza atividades maliciosas secretamente em computadores infectados.
🤔 Como o Wacatac se espalha?
Ele se espalha principalmente por meio de e-mails de spam e ‘cracks’ de software falsificado, enganar os usuários para que baixem anexos infectados ou instalem software pirata, o que leva ao comprometimento do sistema.
🤔 Que danos o Wacatac pode causar?
Wacatac pode atrapalhar significativamente o computador e a vida digital do usuário, roubar informações confidenciais, como credenciais de login e dados financeiros, arriscando violações de privacidade e perdas financeiras substanciais.
Preciso de sua ajuda para compartilhar este artigo.
É a sua vez de ajudar os outros. Este artigo foi elaborado para ajudar pessoas como você. Use os botões abaixo para compartilhar isso em suas plataformas de mídia social preferidas, como o Facebook, Twitter, ou Reddit.
Brendan Smith




Deixe um comentário