Verification.exe是一個惡意行程 在 Windows 系統上發現. 它可能充當礦工,或在惡意的同時偽裝成合法的. 該惡意軟體旨在在受感染的系統上執行各種有害操作. 此類行為包括資料竊取, 部署更多惡意軟體, 以及促進攻擊者未經授權的存取和控制.
驗證.exe概述
Verification.exe 特洛伊木馬是一種有害程序, 可能會導致各種問題 在您受感染的電腦上. 它可用於竊取個人數據, 安裝其他惡意軟體, 並向攻擊者提供未經授權的訪問. 該木馬進行各種惡意活動, 例如 下載並安裝其他惡意軟體, 利用您的計算機進行點擊欺詐, 記錄擊鍵, 並追蹤造訪過的網站.
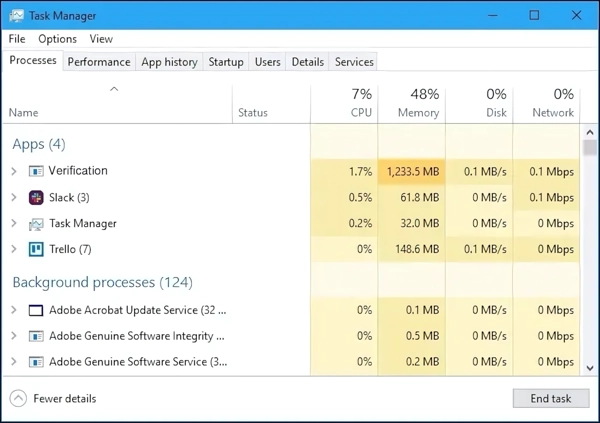
工作管理員中的Verification.exe進程
它還可以傳輸您的電腦訊息, 例如使用者名稱和瀏覽記錄, 遠端惡意實體, 授予對您的 PC 的遠端存取權限, 展示廣告, 並重定向瀏覽器搜尋查詢. 另外, 它可以利用您的電腦資源 用於加密貨幣挖礦. 了解該木馬的潛在威脅並採取措施保護您的電腦免受此類攻擊至關重要.
威脅摘要
| 姓名 | 驗證.exe |
| 威脅類型 | 木馬病毒 |
| 細節 | 竊取個人數據, 帶來其他惡意程序, 破壞系統安全, 可以開採加密貨幣. |
該惡意軟體選擇 Verification.exe 名稱的原因相當簡單 – 與其他後台程式融合. 這通常會讓用戶認為它是合法的. 然而, 當佔用太多系統資源時, 或無論正在運行什麼程式都運行, 那麼是時候拉警報了.
我是怎麼被感染的?
Verification.exe 可以透過多種方式滲透您的系統. 一種標準方法是透過 惡意廣告 瀏覽網路時可能會出現. 這些廣告可能會誘騙您點擊連結或下載包含該特洛伊木馬的附件. 惡意軟體傳播的另一種方式是透過垃圾郵件, 其中可能包含受感染的附件. 它還可以利用您的作業系統或軟體漏洞來存取您的系統.
另一種分發方法是透過盜版軟體或非法下載. 大多數盜版軟體都需要強制 停用安全軟體 在設備上. 這是因為駭客工具的機制與惡意軟體的機制相似, 使其成為傳播的理想選擇. 所以, 假設您正在從不受信任的來源下載軟體或參與軟體盜版. 在那種情況下, 你正在將你的系統置於危險之中.
使用 Gridinsoft 反惡意軟體移除 Verification.exe
從那時起我們就一直在我們的系統上使用這個軟體, 而且在檢測病毒方面一直很成功. 它阻止了最常見的木馬 從我們的測試中可以看出 與軟體, 我們向您保證,它可以刪除 Verification.exe 以及其他隱藏在您電腦上的惡意軟體.

使用 Gridinsoft 刪除惡意威脅, 請依照以下步驟操作:
1. 首先下載 Gridinsoft Anti-Malware, 透過下面的藍色按鈕或直接從官方網站訪問 網格軟體.
2.一旦 Gridinsoft 安裝文件 (安裝-gridinsoft-fix.exe) 已下載, 透過點擊該檔案來執行它. Follow the installation setup wizard's instructions diligently.

3. 訪問 "掃描選項卡" on the application's start screen and launch a comprehensive "全碟掃描" 檢查您的整台計算機. 這種包容性掃描涵蓋了內存, 啟動項, 註冊表, 服務, 司機, 和所有文件, 確保它檢測到隱藏在所有可能位置的惡意軟體.
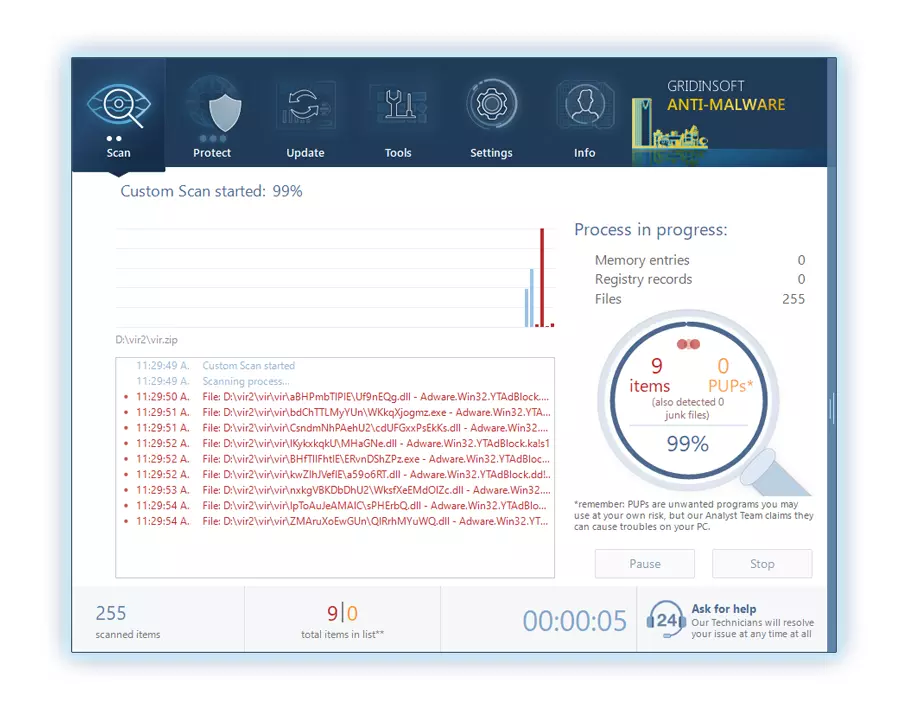
要有耐心, as the scan duration depends on the number of files and your computer's hardware capabilities. 利用這段時間放鬆或處理其他任務.
4. 完成後, 反惡意軟體將提供一份詳細報告,其中包含您 PC 上偵測到的所有惡意專案和威脅.
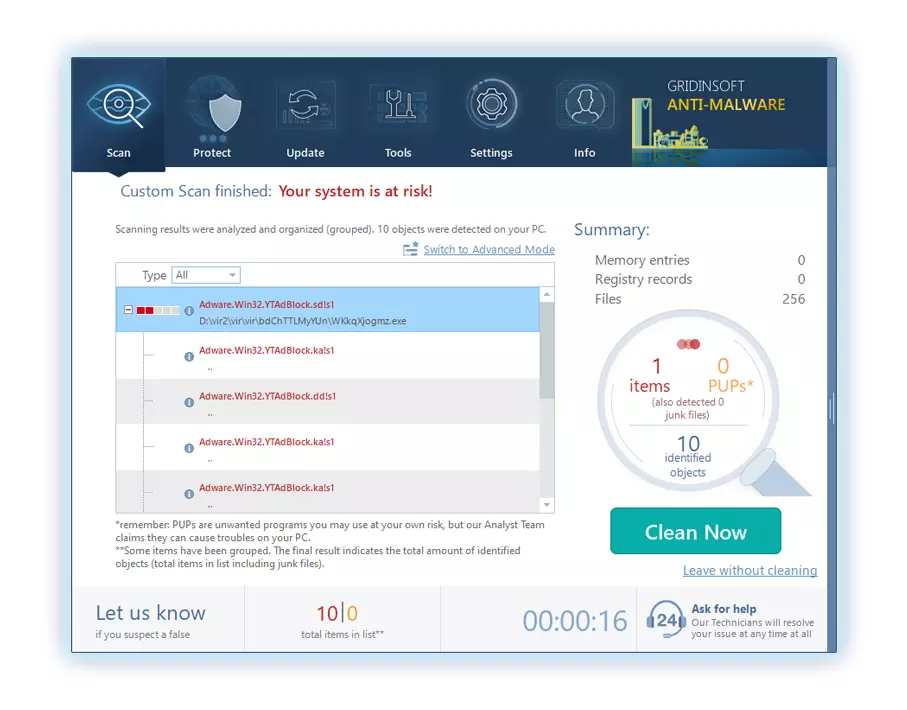
5. 從報告中選擇所有已識別的項目,然後放心地單擊 "立即清潔" 按鈕. 此操作將從您的電腦中安全地刪除惡意文件, 將它們轉移到反惡意軟體程式的安全隔離區,以防止任何進一步的有害行為.
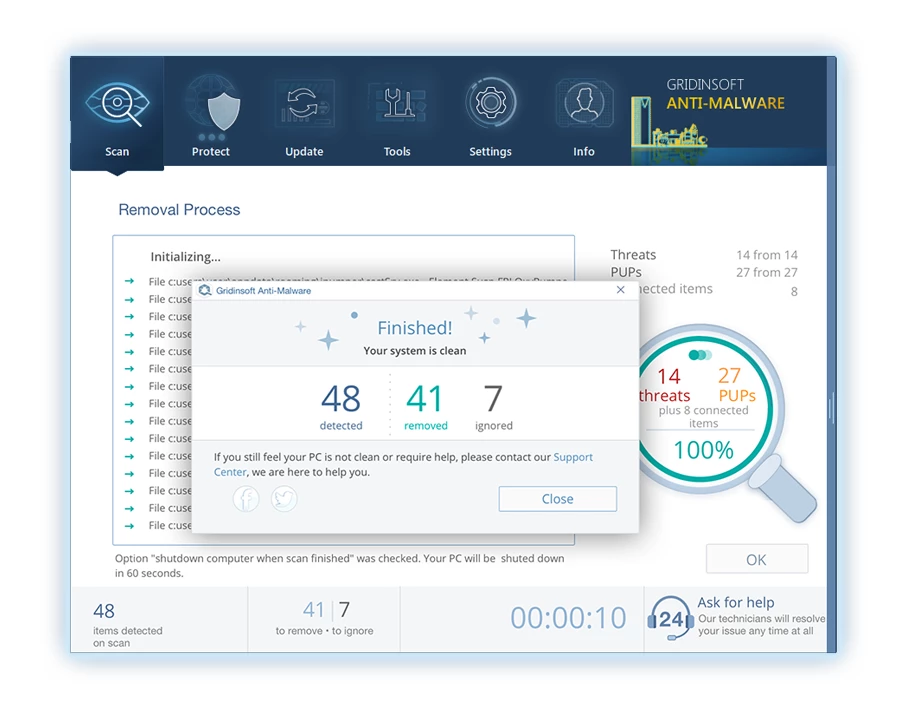
6. 如果出現提示, 重新啟動電腦以完成完整的系統掃描過程. 此步驟對於確保徹底消除任何剩餘威脅至關重要. 重啟後, Gridinsoft Anti-Malware 將會開啟並顯示一則訊息,確認 掃描完成.
請記住 Gridinsoft 提供 6 天免費試用. 這意味著您可以免費利用試用期體驗軟體的全部優勢,並防止您的系統將來受到任何惡意軟體感染. Embrace this opportunity to fortify your computer's security without any financial commitment.






發表評論