Si tu ordenador te avisa con el troyano:Win32/Smokeloader!nombre de detección pz, it’s a critical sign of danger. This detection indicates ransomware, which encrypts your files and demands a ransom for their decryption. Immediate action and specific steps are necessary to remove this malware promptly.
El troyano:Win32/Smokeloader!pz virus is commonly detected after engaging in risky activities on your computer, such as opening suspicious emails, clicking on online ads, or downloading software from unreliable sources. Once detected, swift action is essential to prevent its harmful effects. Delaying can lead to severe damage, so it’s crucial to act quickly.
Understanding Trojan:Win32/Smokeloader!pz Virus
This ransomware targets the files on your computer, encrypts them, and then demands a ransom for a decryption key. In addition to locking your files, troyano:Win32/Smokeloader!pz significantly damages your system’s functionality. It alters network settings to block access to removal guides and prevent the download of anti-malware solutions. A veces, it may even stop anti-malware programs from launching.
Key Features
The following are some of the primary actions of the Trojan:Win32/Smokeloader!pz malware on an infected computer:
- Behavioral detection: Executable code extraction – unpacking.
- Unconventional language in binary resources: Punjabi.
- Authenticode signature is invalid.
- Behavioral detection: Code injection techniques like Process Hollowing and Inter-process.
- Encrypts files, haciéndolos inaccesibles.
- Blocks execution of anti-malware software.
- Prevents the installation of antivirus programs.
Ransomware remains a significant threat, representing one of the most severe types of viruses affecting individuals and businesses alike. The encryption algorithms used (typically RHA-1028 or AES-256) are robust, with decryption through brute force nearly impossible. Despite the power of this malware, it does not execute its actions instantly; it may take several hours to encrypt all your files. De este modo, detecting Trojan:Win32/Smokeloader!pz should be a clear signal to begin the removal process immediately.
troyano:Win32/Smokeloader!pz Spreads
El troyano:Win32/Smokeloader!pz spreads via typical methods shared with other malware types. These include deceptive websites offering free software downloads, phishing emails pretending to be legitimate notifications, and malicious tools. Phishing emails, a newer strategy, may appear as ordinary updates about shipments or bank services but contain harmful attachments or links leading to malicious websites.
Malicious email message. This one tricks you into opening the phishing website.
Avoiding it looks quite uncomplicated, sin embargo, still demands a lot of attention. Malware can hide in different places, and it is better to stop it even before it goes into your computer than to trust in an anti-malware program. Simple cybersecurity knowledge is just an important item in the modern world, even if your relationship with a computer remains on YouTube videos. That can keep you a lot of time and money which you would certainly spend while searching for a fix guide.
Technical Details
| bkav | W32.AIDetectMalware |
| leonico | Trojan.Win32.SmokeLoader.4!do |
| tehtris | Generic.Malware |
| MicroWorld-eScan | Trojan.GenericKD.70612133 |
| ojo de fuego | Generic.mg.284ec46a8277bda8 |
| CAT-QuickHeal | Ransom.Stop.P5 |
| Skyhigh | BehavesLike.Win32.Lockbit.dm |
| ALYac | Trojan.GenericKD.70612133 |
| cilance | unsafe |
| Canción para | Trojan.Win32.Save.a |
| K7AntiVirus | troyano ( 005aafe61 ) |
| Alibaba | troyano:Win32/SmokeLoader.cfaee45c |
| K7GW | troyano ( 005aafe61 ) |
| Cibertemporada | malicious.78f4e3 |
| Estará escondido | Trojan.Generic.D43574A5 |
| Symantec | ML.Atributo.Alta Confianza |
| Elástico | malicioso (alta confianza) |
| CASO-NOD32 | a variant of Win32/Kryptik.HVKJ |
| Bastante | Malicioso (puntaje: 100) |
| ÁPEX | Malicioso |
| almejav | Win.Packer.pkr_ce1a-9980177-0 |
| Kaspersky | HEUR:Trojan.Win32.Chapak.gen |
| Bitdefender | Trojan.GenericKD.70612133 |
| avast | Win32:PWSX-gen [trj] |
| Tencent | Trojan.Win32.Obfuscated.gen |
| Sofos | Troj/Krypt-VK |
| F-Secure | Trojan.TR/Crypt.Agent.kakul |
| DrWeb | Trojan.PWS.Stealer.34727 |
| VIPRE | Trojan.GenericKD.70612133 |
| TrendMicro | Trojan.Win32.SMOKELOADER.YXDK3Z |
| Trapmine | malicious.high.ml.score |
| Emsisoft | Trojan.GenericKD.70612133 (B) |
| centinelauno | IA estática – PE malicioso |
| Jiangmin | Trojan.Chapak.rrw |
| Varist | W32/Kryptik.LDY.gen!eldorado |
| Avira | TR/Crypt.Agent.kakul |
| Antiy-AVL | Trojan/Win32.Caynamer |
| reysoft | Win32.Troj.Agent.cks |
| microsoft | troyano:Win32/Smokeloader!pz |
| ZoneAlarm | HEUR:Trojan.Win32.Chapak.gen |
| Gdatos | Trojan.GenericKD.70612133 |
| Detected | |
| AhnLab-V3 | Malware/Win.RansomX-gen.R625969 |
| McAfee | Artemisa!284EC46A8277 |
| MÁXIMO | malware (ai score=85) |
| VBA32 | BScope.Trojan.Yakes |
| Malwarebytes | Trojan.MalPack.GS |
| Panda | Trj/Genetic.gen |
| TrendMicro-HouseCall | Trojan.Win32.SMOKELOADER.YXDK3Z |
| Creciente | Trojan.SmokeLoader!1.EB63 (CLASSIC) |
| Ícaro | Trojan.Win32.Azorult |
| MaxSecure | Trojan.Malware.73643692.susgen |
| Fortinet | W32/GenKryptik.ERHN!tr |
| AVG | IDP.Genérico |
| DeepInstinct | MALICIOUS |
| Multitud de huelga | ganar/malicious_confidence_100% (W.) |
How to remove?
troyano:Win32/Smokeloader!pz malware is very hard to eliminate manually. It stores its data in several places throughout the disk and can get back itself from one of the parts. Además, varias alteraciones en el registro de Windows, configuraciones de red, and also Group Policies are pretty hard to discover and return to the initial. It is better to use a specific app – exactamente, an anti-malware tool. Antimalware de GridinSoft will fit the best for malware elimination goals.
Eliminar troyano:Win32/Smokeloader!pz with Gridinsoft Anti-Malware
También hemos estado utilizando este software en nuestros sistemas desde entonces., y siempre ha tenido éxito en la detección de virus.. Ha bloqueado los troyanos más comunes como mostrado en nuestras pruebas con el software, y te aseguramos que puede eliminar el troyano:Win32/Smokeloader!pz as well as other malware hiding on your computer.

Para utilizar Gridinsoft para eliminar amenazas maliciosas, sigue los pasos a continuación:
1. Comience descargando Gridinsoft Anti-Malware, accesible a través del botón azul a continuación o directamente desde el sitio web oficial gridinsoft.com.
2.Una vez que el archivo de instalación de Gridinsoft (setup-gridinsoft-fix.exe) se descarga, ejecutarlo haciendo clic en el archivo. Follow the installation setup wizard's instructions diligently.

3. Acceder al "Pestaña Escanear" on the application's start screen and launch a comprehensive "Análisis completo" para examinar toda su computadora. Este escaneo inclusivo abarca la memoria., elementos de inicio, el registro, servicios, conductores, y todos los archivos, asegurando que detecta malware oculto en todas las ubicaciones posibles.
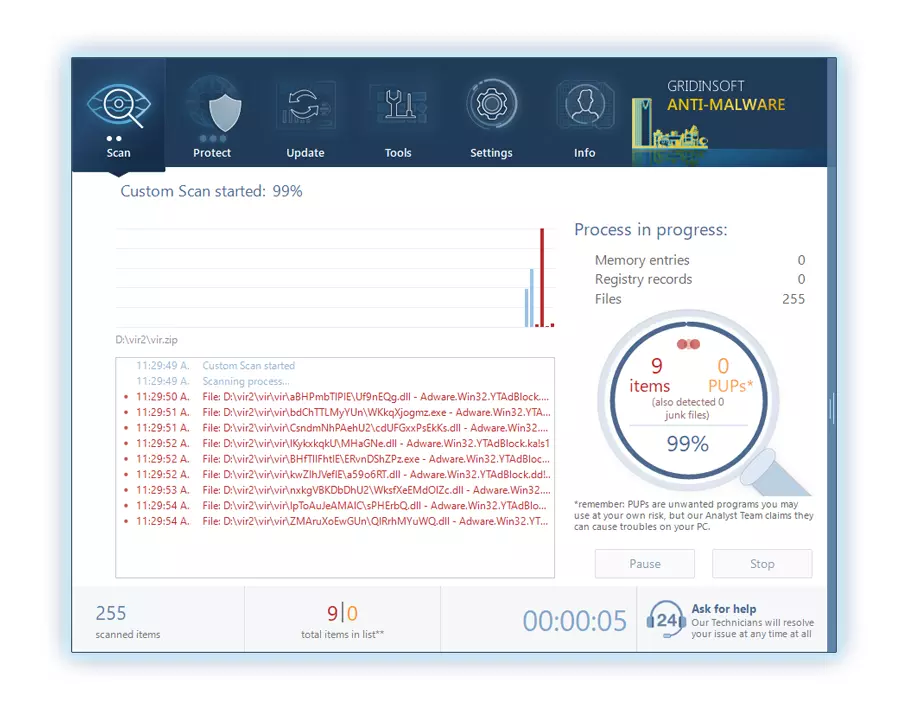
Ser paciente, as the scan duration depends on the number of files and your computer's hardware capabilities. Utilice este tiempo para relajarse o atender otras tareas..
4. Al finalizar, Anti-Malware presentará un informe detallado que contiene todos los elementos maliciosos y amenazas detectados en su PC.
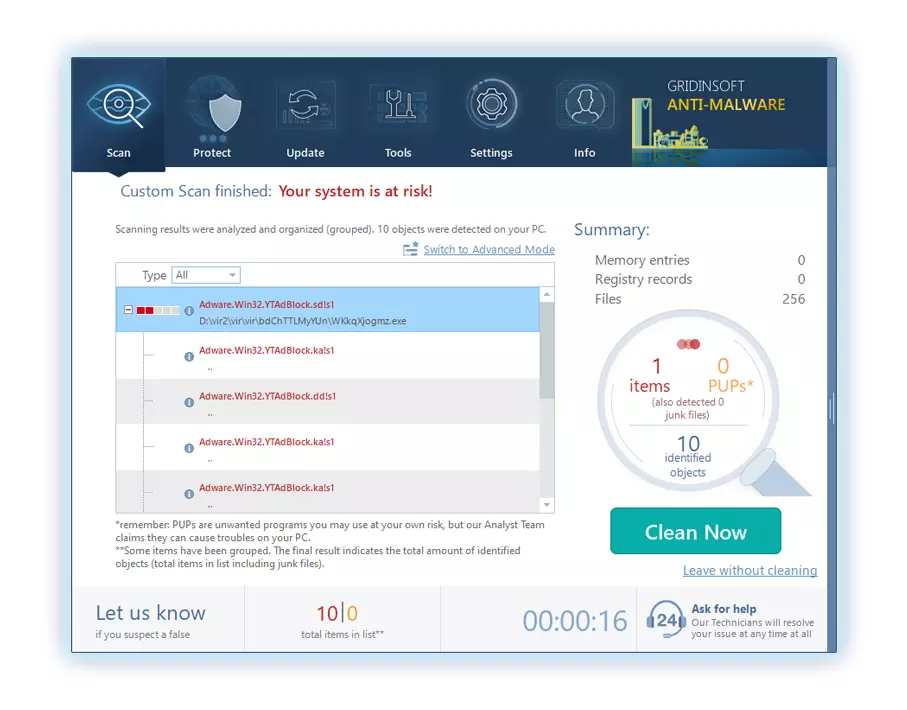
5. Seleccione todos los elementos identificados del informe y haga clic con confianza en el "Limpio ahora" botón. Esta acción eliminará de forma segura los archivos maliciosos de su computadora., transfiriéndolos a la zona de cuarentena segura del programa antimalware para evitar futuras acciones dañinas.
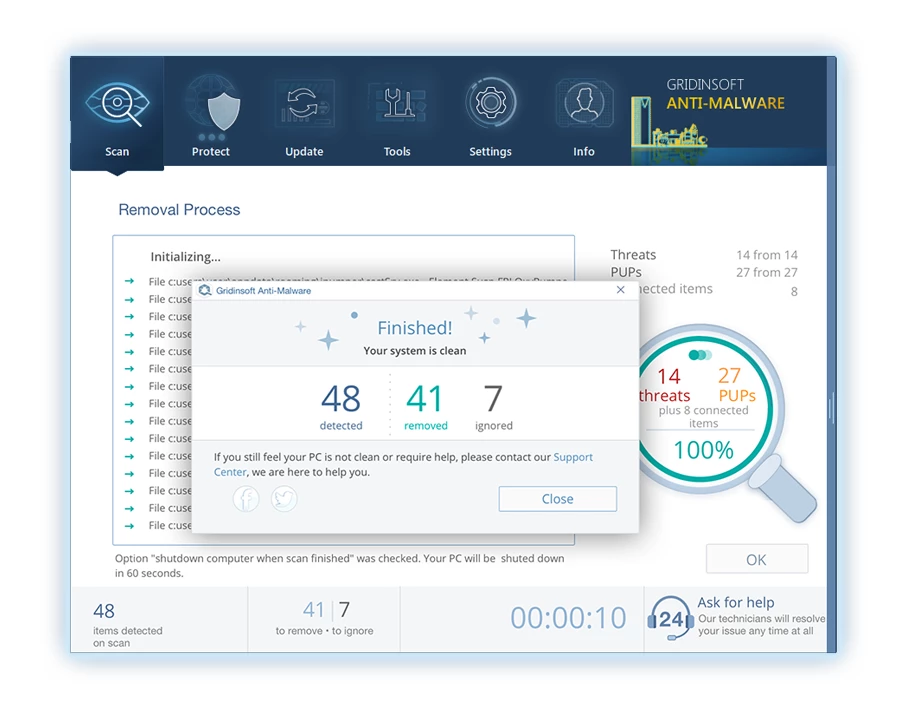
6. Si se le solicita, reinicie su computadora para finalizar el procedimiento de escaneo completo del sistema. Este paso es crucial para garantizar la eliminación completa de cualquier amenaza restante.. Después del reinicio, Gridinsoft Anti-Malware se abrirá y mostrará un mensaje confirmando la finalización del escaneo.
Recuerde Gridinsoft ofrece una prueba gratuita de 6 días. Esto significa que puede aprovechar el período de prueba sin costo alguno para experimentar todos los beneficios del software y prevenir futuras infecciones de malware en su sistema.. Embrace this opportunity to fortify your computer's security without any financial commitment.




Deja un comentario