Trojan Wacatac is identified by Microsoft Defender as encompassing a variety of threats that blend spyware capabilities with the ability to deliver malware. Recognized for its high risk, Wacatac demands cautious handling due to its dangerous nature.
Understanding Wacatac
Wacatac serves as a label for a broad spectrum of malicious software characterized by its spyware functionality and its role as a malware distributor or dropper. This dual functionality is prevalent in many modern malware instances, making Wacatac detections increasingly common.
Occasionally, what is detected might primarily be a dropper rather than spyware or a data stealer. Droppers typically gather system information to identify the targeted device, a behavior Microsoft Defender may interpret as data collection. While this data gathering is less comprehensive, it underscores the rationale behind the detection.
Threat Overview
| Nombre | troyano:Win32/Wacatac |
| Behavior | Data theft, Malware distribution |
| Malware Category | software espía, Infostealer, Banking Trojan, Dropper |
| Transmission Methods | Malicious email attachments, unauthorized software from non-official sources |
| Variants | troyano:Win32/wacatac.b!ml, troyano:Win32/Wacatac.H!ml, troyano:Script/Wacatac.H!ml |
The Risks Posed by Trojan:Win32/Wacatac
The primary threats of Wacatac include its spyware capabilities — alarming for user privacy as it captures passwords, cookie files, and session tokens. Its role as a dropper exacerbates the risk by introducing additional malware, thus enhancing the attackers’ gain.
Certain Wacatac variants target specific areas such as cryptocurrency wallets or online banking, trading general theft for the potential of significant financial harm. Nonetheless, attackers can easily couple standard spyware with banking trojans, cryptostealers, or ransomware as a secondary payload.
Malware Families Detected as Trojan Wacatac
Wacatac is not confined to a single malware family but includes several types recognized by their shared characteristics. Microsoft Defender frequently identifies the following families under the Wacatac designation:
| Amadey Dropper | Currently among the most active malwares, used to distribute Vidar, RedLine stealers, and STOP/Djvu ransomware. Occasionally delivers cryptominers while collecting basic system information. |
| Gozi Stealer | Initially a data stealer, Gozi was later enhanced with malware distribution capabilities. It primarily functions as spyware. |
| Emotet (Epoch 4 variants) | A notorious malware known for combining dropper and stealer roles. While Defender typically categorizes it as Sabsik, changes in the Epoch 4 variant likely altered its signature to resemble Wacatac more closely. |
| QakBot | A long-standing malware primarily used in targeted attacks for reconnaissance and lateral movement. Its network was recently dismantled, potentially signaling an imminent resurgence. |
| FormBook | Also known as xLoader, active since 2016, it combines stealer and dropper functions but is less infamous than Emotet. |
Eliminating the Wacatac Trojan
Wacatac establishes deep roots upon infection, making manual removal challenging. This stealthy behavior is typical for malware seeking to avoid detection. As such, utilizing an anti-malware tool is advisable for thorough removal.
Antimalware de GridinSoft stands out as an effective solution, thanks to its constantly updated database and sophisticated heuristic detection capabilities, ensuring the identification and elimination of the latest malware threats.
Remove Wacatac Trojan with Gridinsoft Anti-Malware
También hemos estado utilizando este software en nuestros sistemas desde entonces., y siempre ha tenido éxito en la detección de virus.. Ha bloqueado los troyanos más comunes como mostrado en nuestras pruebas con el software, and we assure you that it can remove Wacatac Trojan as well as other malware hiding on your computer.

Para utilizar Gridinsoft para eliminar amenazas maliciosas, sigue los pasos a continuación:
1. Comience descargando Gridinsoft Anti-Malware, accesible a través del botón azul a continuación o directamente desde el sitio web oficial gridinsoft.com.
2.Una vez que el archivo de instalación de Gridinsoft (setup-gridinsoft-fix.exe) se descarga, ejecutarlo haciendo clic en el archivo. Follow the installation setup wizard's instructions diligently.

3. Acceder al "Pestaña Escanear" on the application's start screen and launch a comprehensive "Análisis completo" para examinar toda su computadora. Este escaneo inclusivo abarca la memoria., elementos de inicio, el registro, servicios, conductores, y todos los archivos, asegurando que detecta malware oculto en todas las ubicaciones posibles.
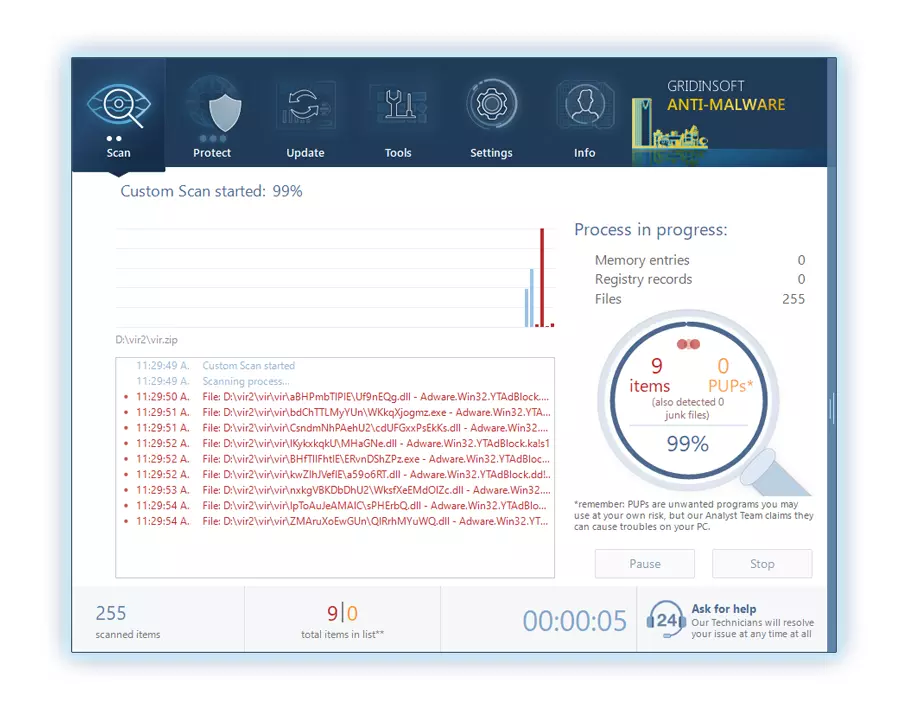
Ser paciente, as the scan duration depends on the number of files and your computer's hardware capabilities. Utilice este tiempo para relajarse o atender otras tareas..
4. Al finalizar, Anti-Malware presentará un informe detallado que contiene todos los elementos maliciosos y amenazas detectados en su PC.
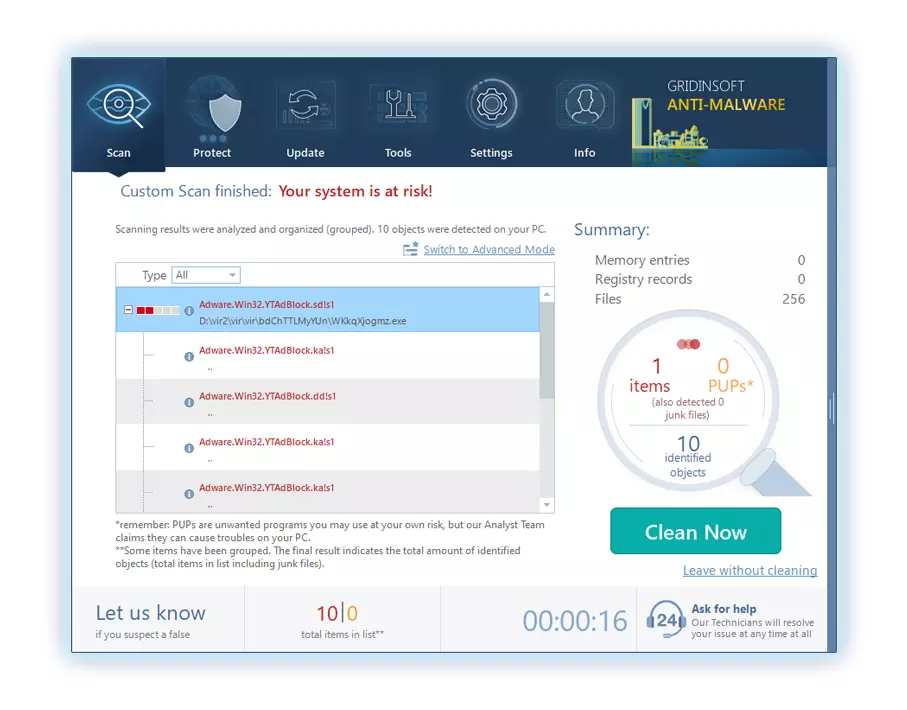
5. Seleccione todos los elementos identificados del informe y haga clic con confianza en el "Limpio ahora" botón. Esta acción eliminará de forma segura los archivos maliciosos de su computadora., transfiriéndolos a la zona de cuarentena segura del programa antimalware para evitar futuras acciones dañinas.
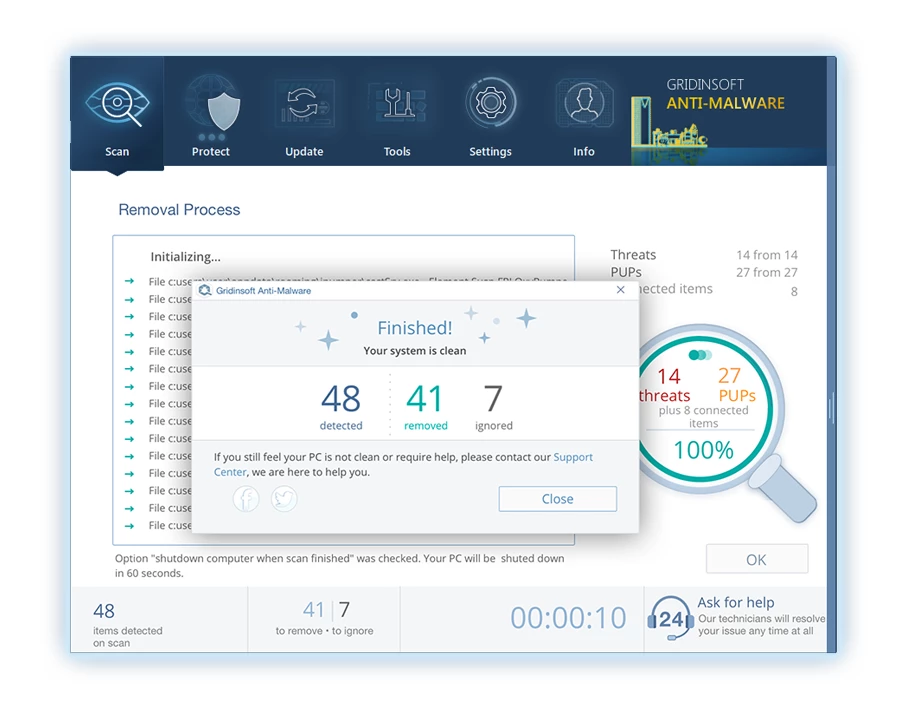
6. Si se le solicita, reinicie su computadora para finalizar el procedimiento de escaneo completo del sistema. Este paso es crucial para garantizar la eliminación completa de cualquier amenaza restante.. Después del reinicio, Gridinsoft Anti-Malware se abrirá y mostrará un mensaje confirmando la finalización del escaneo.
Recuerde Gridinsoft ofrece una prueba gratuita de 6 días. Esto significa que puede aprovechar el período de prueba sin costo alguno para experimentar todos los beneficios del software y prevenir futuras infecciones de malware en su sistema.. Embrace this opportunity to fortify your computer's security without any financial commitment.
Preguntas frecuentes
🤔 What is Trojan Wacatac?
Wacatac, also known as Trojan:Win32/Wacatac, is malware that performs malicious activities covertly on infected computers.
🤔 How does Wacatac spread?
It spreads mainly through spam emails and counterfeit software ‘cracks’, tricking users into downloading infected attachments or installing pirated software, which leads to system compromise.
🤔 What harm can Wacatac cause?
Wacatac can significantly disrupt both the computer and the user’s digital life, stealing sensitive information like login credentials and financial data, risking privacy breaches and substantial financial loss.
Necesito tu ayuda para compartir este artículo.
It’s your turn to assist others. This article was crafted to aid individuals like you. Use the buttons below to share this on your preferred social media platforms like Facebook, Gorjeo, o Reddit.
Brendan Smith




Deja un comentario