¿Qué es el virus bgzq??
BGZQ un tipo de ransomware STOP/Djvu, cifra archivos en computadoras, haciéndolos inaccesibles. Se dirige a una variedad de tipos de archivos, Añadir un “.bgzq” extensión a ellos, que hace que los archivos sean inutilizables sin una clave de descifrado.
Después de infectar un sistema, BGZQ exige un rescate en bitcoin para descifrar archivos. Las víctimas encuentran un “_readme.txt” Guía en escritorios y dentro de las carpetas que les indican sobre cómo realizar el pago, Aunque el pago no garantiza la recuperación.
El virus emplea el Algoritmo de cifrado SALSA20, lo que complica los esfuerzos de descifrado sin la cooperación del atacante. Sin embargo, Si BGZQ no puede conectarse a su servidor antes de iniciar el cifrado, Utiliza una clave estándar fuera de línea, ofreciendo una vía potencial para el descifrado.
Abajo, Una imagen muestra la apariencia de archivos cifrados, marcado por el “.bgzq” extensión:
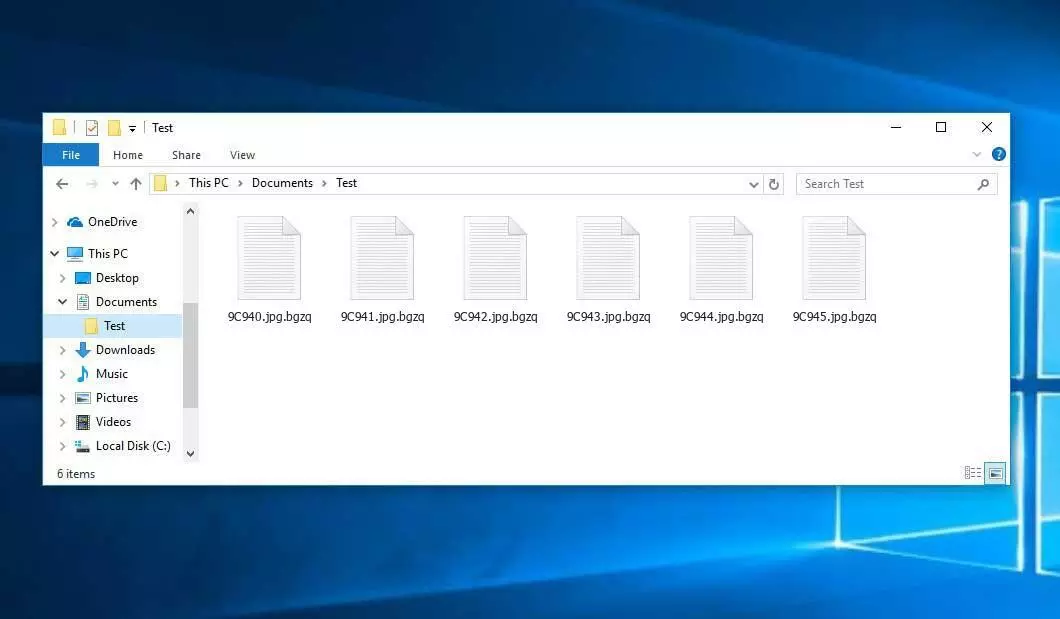
Secuestro de datos: Archivos bgzq
| Nombre | Virus bgzq |
| Familia 1 | Parada / ransomware DJVU |
| Extensión | .bgzq |
| Nota de ransomware | _readme.txt |
| Rescate | De $499 a $999 (en bitcoins) |
| Contacto | support@freshingmail.top, datarestorehelpyou@airmail.cc |
| Síntomas |
|
| Recuperación | Iniciar recuperación con un integral exploración antivirus. Aunque no todos los archivos pueden ser recuperables, Nuestra guía describe varios métodos potenciales para recuperar el acceso a los archivos cifrados. |
Descripción general del virus BGZQ
El ransomware BGZQ ejecuta un conjunto de procedimientos en la computadora de una víctima a su llegada. Lanza winupdate.exe como uno de los procesos iniciales, que muestra un indicador de actualización de Windows fraudulento durante el ataque para convencer a la víctima que su PC se está desacelerando debido a una actualización de Windows.
Mientras tanto, El ransomware ejecuta otro proceso (nombrado con 4 chars aleatorios), que comienza a escanear la computadora para archivos de destino y encriptarlos. Luego elimina las copias de la sombra de volumen del sistema utilizando el siguiente comando CMD:
vssadmin.exe Eliminar sombras /todo /tranquilo
Una vez eliminado, se hace imposible recuperar el estado anterior de la computadora utilizando puntos de restauración del sistema. Los operadores de ransomware eliminan cualquier enfoque incorporado de Windows que pueda ayudar a la víctima a restaurar los archivos de forma gratuita. Además, Modifican el archivo de hosts de Windows al agregarle una lista de dominios, redirigirlos a la IP localhost, que da como resultado un error dns_probe_finished_nxdomain cuando la víctima intenta abrir uno de los sitios web bloqueados.
Hemos observado que el ransomware intenta restringir los sitios web de publicar varias guías prácticas para usuarios de computadoras. Claramente, limitando dominios específicos, Los atacantes intentan evitar que las víctimas accedan a la información en línea relevante y útil relacionada con los ataques de ransomware. El virus también almacena dos archivos .txt en la computadora de la víctima que proporciona información relacionada con el ataque: la clave pública de esta víctima y una identificación personal, nombrado bowsakkdestx.txt y Personalid.txt.
Después de todas estas modificaciones, El malware no se detiene. Variantes de Stop/DJVU a menudo implementan el troyano de robo de contraseñas Vidar en sistemas comprometidos, una amenaza con una vasta lista de capacidades, incluido:
- Infiltrarse y ejecutar malware en la computadora de la víctima para obtener acceso no autorizado.
- Obtener acceso no autorizado a las credenciales de inicio de sesión de Steam, Telegrama, y Skype.
- Manipular y ver archivos en la computadora de la víctima sin su consentimiento.
- Robar billeteras de criptomonedas del sistema de la víctima.
- Otorgando a los piratas informáticos control remoto sobre la computadora de la víctima para varios fines maliciosos.
- Extraer información confidencial como cookies de navegador, Contraseñas guardadas, e navegando en la historia.
El algoritmo de criptografía en stop/djvu ransomware es salse20. Entonces, Una vez que cifra sus datos con una clave de descifrado en línea, Las posibilidades de recuperar sus archivos se vuelven bastante bajas. Esta clave es única para cada víctima, y encontrar uno adecuado tomaría una cantidad de tiempo poco práctica.
Recuperar la clave en línea de otra manera también es casi imposible. Los piratas informáticos difundieron la infección BGZQ en el servidor donde se almacena. Para recibir el código de descifrado, El pago debe ser $999. Para detalles de pago, Las víctimas deben comunicarse con los hackers por correo electrónico (support@fishmail.top).
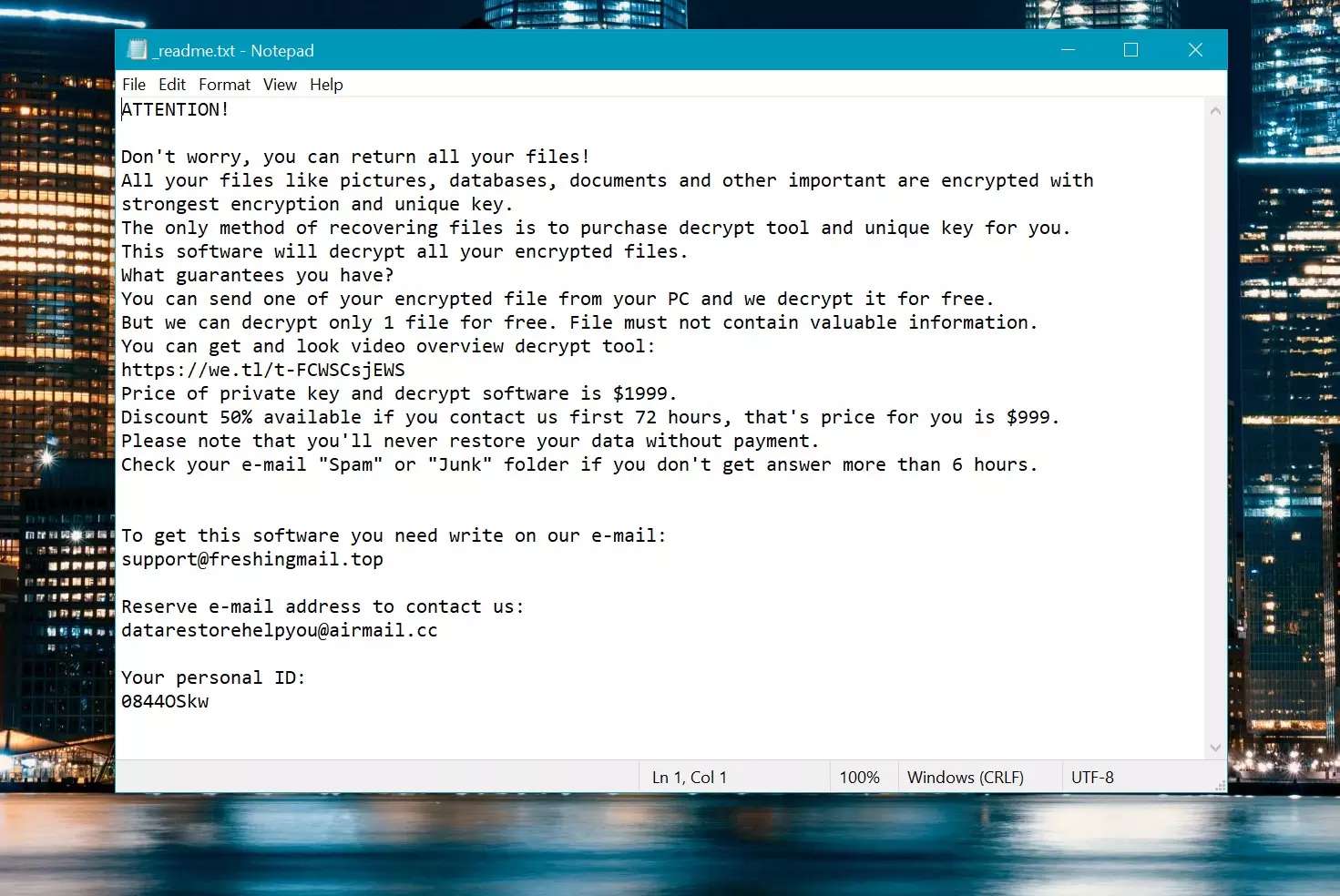
Nota de rescate: _readme.txt
Cómo quitar?
Eliminar el virus BGZQ con el anti-malware GridinSoft
También hemos estado utilizando este software en nuestros sistemas desde entonces., y siempre ha tenido éxito en la detección de virus.. Ha bloqueado el ransomware más común como mostrado en nuestras pruebas con el software, y le aseguramos que puede eliminar el virus BGZQ, así como otro malware que se esconde en su computadora..

Para utilizar Gridinsoft para eliminar amenazas maliciosas, sigue los pasos a continuación:
1. Comience descargando Gridinsoft Anti-Malware, accesible a través del botón azul a continuación o directamente desde el sitio web oficial gridinsoft.com.
2.Una vez que el archivo de instalación de Gridinsoft (setup-gridinsoft-fix.exe) se descarga, ejecutarlo haciendo clic en el archivo. Follow the installation setup wizard's instructions diligently.

3. Acceder al "Pestaña Escanear" on the application's start screen and launch a comprehensive "Análisis completo" para examinar toda su computadora. Este escaneo inclusivo abarca la memoria., elementos de inicio, el registro, servicios, conductores, y todos los archivos, asegurando que detecta malware oculto en todas las ubicaciones posibles.
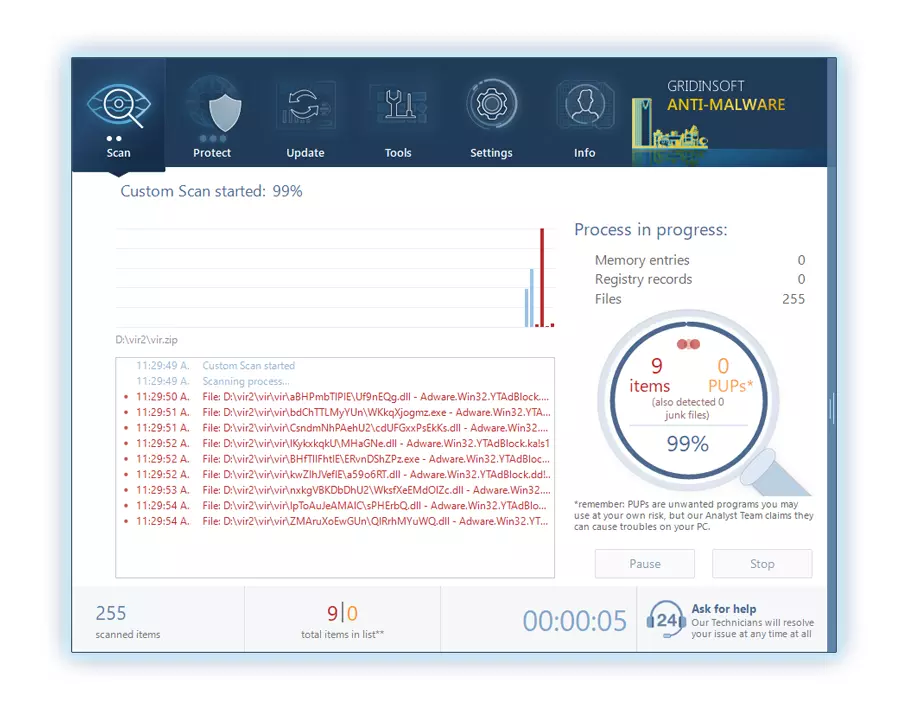
Ser paciente, as the scan duration depends on the number of files and your computer's hardware capabilities. Utilice este tiempo para relajarse o atender otras tareas..
4. Al finalizar, Anti-Malware presentará un informe detallado que contiene todos los elementos maliciosos y amenazas detectados en su PC.
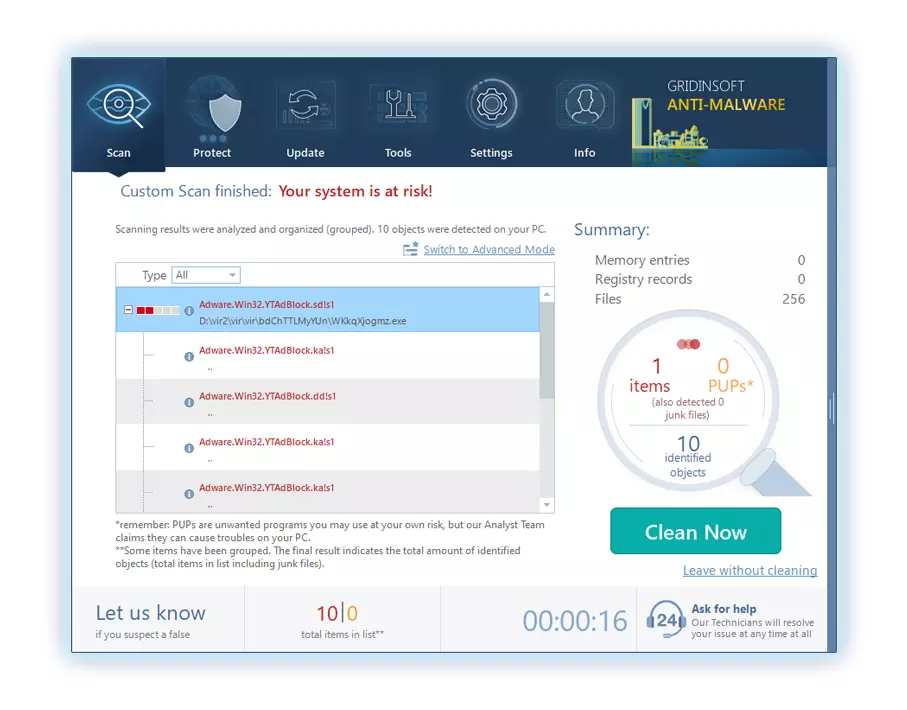
5. Seleccione todos los elementos identificados del informe y haga clic con confianza en el "Limpio ahora" botón. Esta acción eliminará de forma segura los archivos maliciosos de su computadora., transfiriéndolos a la zona de cuarentena segura del programa antimalware para evitar futuras acciones dañinas.
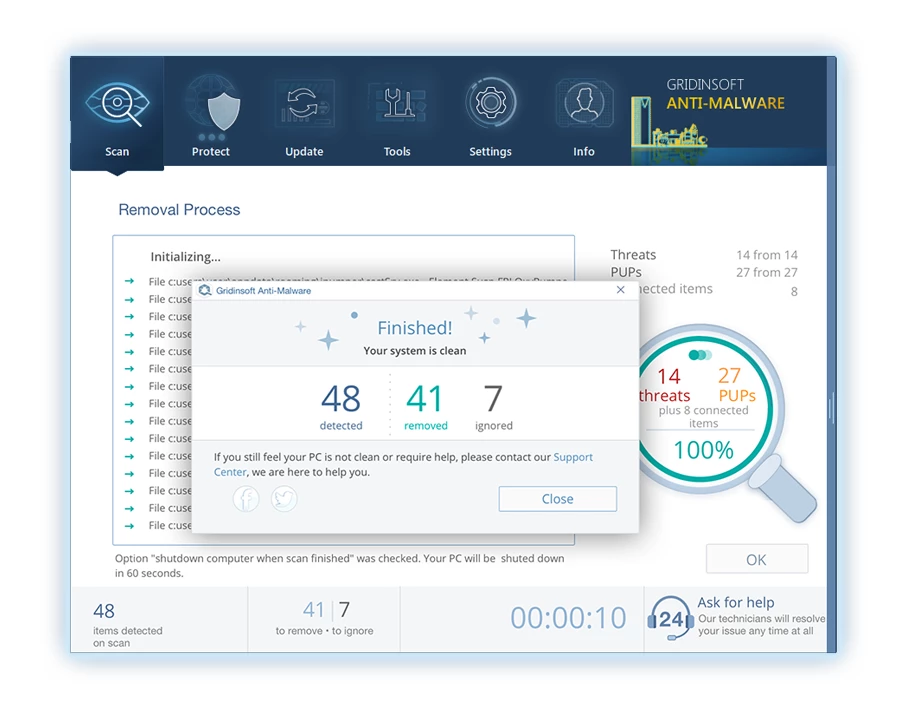
6. Si se le solicita, reinicie su computadora para finalizar el procedimiento de escaneo completo del sistema. Este paso es crucial para garantizar la eliminación completa de cualquier amenaza restante.. Después del reinicio, Gridinsoft Anti-Malware se abrirá y mostrará un mensaje confirmando la finalización del escaneo.
Recuerde Gridinsoft ofrece una prueba gratuita de 6 días. Esto significa que puede aprovechar el período de prueba sin costo alguno para experimentar todos los beneficios del software y prevenir futuras infecciones de malware en su sistema.. Embrace this opportunity to fortify your computer's security without any financial commitment.
Guía de vídeo
Cómo descifrar archivos .bgzq?
Primero, Intenta eliminar el “.bgzq” extensión de algunos archivos grandes y luego abrirlos. Este malware lucha con el cifrado de archivos grandes. El virus no pudo bloquear el archivo al acceso o encontró un error y omitió agregar el marcador de archivo. Si sus archivos exceden 2 GB de tamaño, el último escenario es más probable.
Los delincuentes publicaron las extensiones más nuevas a fines de agosto 2019 Después de hacer varios cambios.
Los cambios por parte de los delincuentes dejaron stopdecrypter sin apoyo, Conduciendo a su reemplazo con el descifrador Emsisoft para el ransomware DJVU desarrollado por Emsisoft.
- Descargue y ejecute la herramienta de descifrado: Descargar herramienta de descifrado. Asegúrese de ejecutar la utilidad de descifrado como administrador y acepte los términos de la licencia que aparecen haciendo clic en el “Sí” botón. Al aceptar los términos de la licencia.
- Seleccione carpetas para el descifrado: El descifrador, por defecto, Selecciona automáticamente directorios en unidades conectadas y de red para el descifrado. Usar el “Agregar” botón para seleccionar ubicaciones adicionales. Dependiendo de la familia de malware, Los descifrantes ofrecen varias opciones, que puede activar o desactivar en la pestaña Opciones. Abajo, Encontrará una lista detallada de las opciones actualmente activas.
- Iniciar el descifrado haciendo clic en el “Descifrar” Botón. Después de agregar todas las ubicaciones deseadas a la lista, haga clic en el “Descifrar” botón para iniciar el proceso de descifrado. El Decryptor le informará al completar el proceso de descifrado. Si es necesario para la documentación, Puede guardar el informe haciendo clic en el “Guardar registro” botón. También es posible copiar el informe a su portapapeles para pegar correos electrónicos o mensajes..
Cómo restaurar archivos .bgzq?
En algunos casos, El ransomware no puede cifrar sus archivos…
El proceso de cifrado de ransomware BGZQ implica cifrar cada archivo byte-by-byte, creando un duplicado, y luego eliminar (No sobrescribir) el archivo original. Esta eliminación significa que el disco físico ya no enumera el archivo en su sistema, Aunque el archivo original permanece en la unidad. El sector que contenía el archivo aún podría contenerlo, Pero dado que el sistema no lo enumera, Los nuevos datos pueden sobrescribirlo. Sin embargo, El software especial puede recuperar sus archivos.
Darse cuenta de que era un algoritmo en línea, Sabía que recuperar mis archivos encriptados era imposible. Mi unidad de copia de seguridad, conectado durante la infección, parecía infectado también. Cada carpeta de mi unidad de copia de seguridad apareció encriptada. A pesar de esto, Logré recuperarme casi 80% de mi almacenamiento de 2tb.
Examinando las carpetas, Encontré notas de rescate en cada. La apertura de algunos reveló que solo los archivos que no estaban en subcarpetas estaban encriptados. Profundizar en subcarpetas en otras carpetas, Descubrí archivos sin cifrar. A diferencia de mis unidades C y D, donde cada carpeta, incluyendo subcarpetas, fue encriptado, Las subcarpetas de mi unidad de respaldo se guardan 80% de mis datos.
Considero encontrar esta escapatoria en mi impulso de respaldo afortunado. Además, Recuperé otro 10% de mis datos de un disco duro en una PC diferente. De este modo, Mi consejo para usar una unidad de copia de seguridad es crear subcarpetas.. Fue en parte suerte, pero también desgracia que el virus golpeó durante las transferencias de archivo desde mi copia de seguridad.
Espero que esta experiencia pueda ayudar a otros en predicamentos similares..
Jamie NewlandRecuperar archivos BGZQ con Photorec
Fotorecia, Diseñado para la recuperación de archivos de discos dañados o eliminación accidental, ahora admite la restauración 400 tipos de archivos, haciéndolo útil después de un ataque BGZQ.
Primero, Descargar fotorec. Es gratis, Pero el desarrollador no ofrece garantía para la restauración de archivos. Photorec viene empaquetado con TestDisk, otra herramienta del mismo desarrollador, Bajo el nombre de Testdisk. Sin embargo, Photorec se incluye dentro del archivo.
Para comenzar Photorec, abrir el “qphotorec_win.exe” archivo. No es necesaria una instalación ya que el programa contiene todos los archivos requeridos., permitiendo que se ejecute desde una unidad USB.







Deja un comentario